Introduction
Zero Trust Network Access (ZTNA) solutions are modern security platforms that enforce the principle of “never trust, always verify.” They authenticate users and devices before granting access to applications, ensuring least-privilege access and reducing risks of lateral movement or data breaches. Unlike traditional VPNs, ZTNA operates at the application layer, providing granular access control and continuous verification for hybrid, cloud, and remote environments.
ZTNA matters because modern enterprises face distributed workforces, cloud adoption, and increased third-party interactions, making perimeter-based security inadequate. Implementing ZTNA provides secure access, visibility, and compliance while improving overall security posture.
Real-world use cases include:
- Secure remote access to internal and cloud applications
- Conditional access for contractors and vendors
- Continuous monitoring of user and device trust
- Reducing lateral movement in case of credential compromise
- Integration with SaaS and private cloud apps for unified security
When evaluating ZTNA solutions, consider:
- Identity verification (SSO, MFA, adaptive authentication)
- Granular, least-privilege access policies
- Integration with IAM, endpoint security, and SIEM
- Real-time monitoring, analytics, and reporting
- Deployment flexibility (cloud, hybrid, on-premises)
- Scalability for hybrid workforces
- Policy management and administrative ease
- Security certifications (SOC 2, ISO 27001, GDPR)
- Vendor support and professional services
- Pricing and total cost of ownership
Best for: Security architects, IT teams, compliance officers, and enterprises managing hybrid or remote workforces with complex access requirements.
Not ideal for: Small organizations with minimal remote access or simple VPN needs; ZTNA may be excessive for such environments.
Key Trends in Zero Trust Network Access (ZTNA)
- Adoption of cloud-native ZTNA for distributed workforces
- Integration with SASE (Secure Access Service Edge) frameworks
- AI-driven continuous trust evaluation and anomaly detection
- Context-aware, adaptive access policies based on risk and device posture
- Device compliance checks before granting access
- Granular application-level access control
- Zero trust coverage extended to SaaS, private cloud, and legacy apps
- Unified visibility and monitoring across users, devices, and applications
- BYOD and contractor access management
- Convergence with endpoint security and SIEM for holistic protection
How We Selected These Tools (Methodology)
- Market adoption and mindshare among IT and security teams
- Feature completeness: identity verification, policy enforcement, continuous trust
- Reliability and performance in enterprise deployments
- Security posture: encryption, SSO/MFA, RBAC, audit logging
- Integration ecosystem: IAM, endpoint security, SIEM, SASE
- Scalability for hybrid, cloud, and global workforce scenarios
- Ease of deployment and policy management
- Vendor support, training, and documentation
- Customer fit across small, mid-market, and enterprise segments
- Value and total cost of ownership
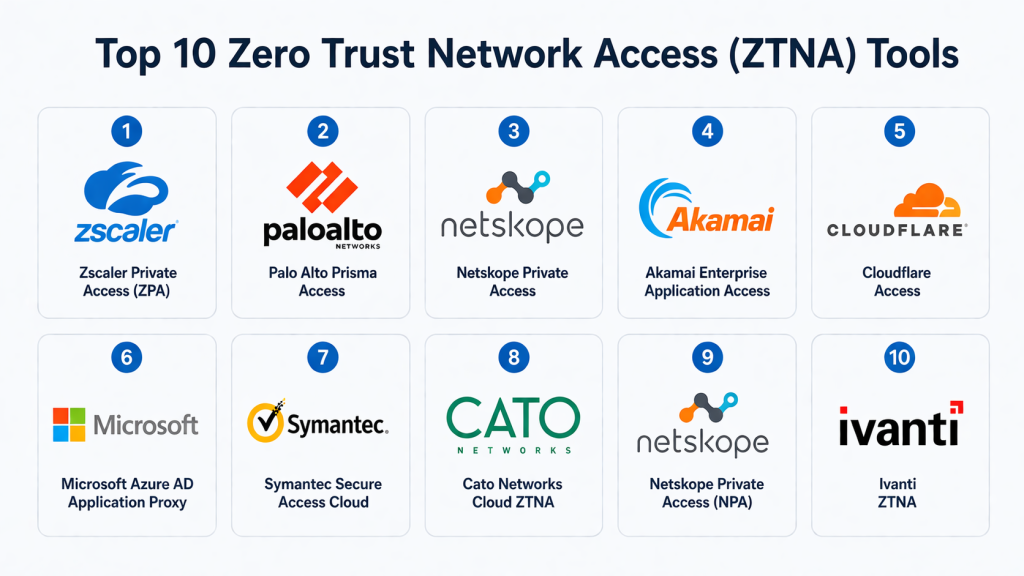
Top 10 Zero Trust Network Access (ZTNA) Tools
#1 — Zscaler Private Access (ZPA)
Short description:
Zscaler Private Access is a cloud-native ZTNA solution providing secure, least-privilege access to internal applications without exposing networks. It is ideal for large, distributed enterprises seeking scalable and policy-driven access.
Key Features
- Cloud-native secure access to applications
- Least-privilege enforcement and adaptive policies
- Continuous user and device verification
- Centralized policy orchestration
- Real-time monitoring and analytics
- Integration with SSO and MFA
- Multi-region scalable deployment
Pros
- Eliminates VPN bottlenecks
- Enterprise-scale deployment capability
Cons
- Premium pricing
- Complex initial configuration
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SSO, MFA, encryption, audit logs, RBAC
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
Integrates with IAM, endpoint security, SIEM, and cloud apps
- Identity providers (SSO/MFA)
- Endpoint detection and response tools
- Analytics and reporting platforms
Support & Community
Professional support, onboarding, and documentation
#2 — Palo Alto Prisma Access
Short description:
Prisma Access delivers ZTNA with cloud security and threat prevention, providing adaptive, policy-driven access to applications for enterprise users.
Key Features
- Cloud-delivered secure access
- Integrated threat prevention
- Adaptive access policies based on context
- Device and user posture verification
- Unified management console
- Real-time monitoring and analytics
Pros
- Enterprise-grade security
- Integration with Palo Alto Networks ecosystem
Cons
- Complex for small teams
- Premium pricing
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SSO, MFA, encryption, audit logs
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- IAM, endpoint security, SIEM, networking tools
Support & Community
Enterprise support and documentation
#3 — Netskope Private Access
Short description:
Netskope Private Access secures both private and SaaS applications with context-aware policies, enabling secure hybrid and remote access.
Key Features
- Identity and device verification
- Adaptive access policies
- Continuous monitoring
- Cloud and SaaS visibility
- Application segmentation
Pros
- Strong SaaS and private app protection
- Context-aware policies
Cons
- Dependent on Netskope ecosystem
- Technical setup requires expertise
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SSO, MFA, encryption
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- IAM, endpoint security, SIEM
- Cloud and collaboration tools
Support & Community
Vendor support and documentation
#4 — Akamai Enterprise Application Access
Short description:
Akamai EAA provides granular ZTNA at the application level, enforcing adaptive policies and minimizing lateral movement risks.
Key Features
- Granular application access control
- Context-aware adaptive policies
- Device posture verification
- Continuous monitoring and logging
Pros
- Reduces lateral movement risks
- Eliminates VPN dependency
Cons
- Enterprise pricing
- Requires careful deployment planning
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SSO, MFA, encryption
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- IAM, endpoint security, SIEM
Support & Community
Professional onboarding and documentation
#5 — Cloudflare Access
Short description:
Cloudflare Access enforces identity-based ZTNA for SaaS and internal apps, integrating with identity providers for secure authentication.
Key Features
- Identity provider enforcement
- MFA and SSO integration
- Real-time policy evaluation
- Lightweight cloud deployment
- Audit logging and reporting
Pros
- Quick deployment and ease of use
- Cost-effective for SMBs and enterprises
Cons
- Offline access limited
- Advanced features require higher tiers
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SSO, MFA, encryption
- SOC 2, GDPR
Integrations & Ecosystem
- Identity providers, logging tools, SIEM
- Cloud applications and collaboration platforms
Support & Community
Vendor documentation and support
#6 — Microsoft Azure AD Application Proxy
Short description:
Azure AD Application Proxy delivers secure access to on-premises apps using Azure AD for authentication and conditional policies.
Key Features
- Conditional access enforcement
- Integration with SSO/MFA
- Device compliance validation
- Audit and reporting
Pros
- Seamless Microsoft ecosystem integration
- Familiar identity management tools
Cons
- Best suited for Microsoft-centric environments
- Limited analytics outside Azure
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SSO, MFA, encryption, audit logs
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Azure AD, Microsoft 365, endpoint security, SIEM
Support & Community
Microsoft support and documentation
#7 — Symantec Secure Access Cloud
Short description:
Symantec Secure Access Cloud provides enterprise ZTNA with real-time monitoring, least-privilege enforcement, and adaptive access.
Key Features
- Least-privilege access enforcement
- Device and identity verification
- Continuous monitoring
- Adaptive access policies
- Application segmentation
Pros
- Enterprise-scale ZTNA
- Real-time threat detection
Cons
- Complex deployment
- Premium pricing
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SSO, MFA, encryption, audit logs
- SOC 2, ISO 27001
Integrations & Ecosystem
- IAM, endpoint security, SIEM
Support & Community
Professional support and services
#8 — Cato Networks Cloud ZTNA
Short description:
Cato Networks integrates ZTNA with SD-WAN and unified policies for distributed enterprise access and monitoring.
Key Features
- Cloud-native ZTNA
- SD-WAN integration
- Centralized policy enforcement
- Analytics and reporting
- Adaptive access evaluation
Pros
- Unified networking and security
- Centralized management
Cons
- More complex than standalone ZTNA
- Premium pricing
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SSO, MFA, encryption
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- IAM, endpoint security, SIEM, cloud apps
Support & Community
Professional support and documentation
#9 — Netskope Private Access (NPA)
Short description:
NPA provides secure ZTNA for private and SaaS apps with context-aware policies and continuous monitoring.
Key Features
- Identity and device verification
- Context-aware adaptive policies
- Continuous monitoring
- Application segmentation
- Analytics dashboards
Pros
- Strong SaaS and private app protection
- Adaptive, context-aware access
Cons
- Requires Netskope ecosystem
- Technical setup required
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SSO, MFA, encryption
- SOC 2, GDPR
Integrations & Ecosystem
- IAM, endpoint security, SIEM
Support & Community
Vendor support and documentation
#10 — Ivanti ZTNA
Short description:
Ivanti ZTNA delivers secure, least-privilege access with continuous risk assessment and adaptive policies for hybrid workforces.
Key Features
- Identity and device verification
- Adaptive, context-aware policies
- Continuous risk evaluation
- Application-level access
- Analytics and monitoring
Pros
- Strong least-privilege enforcement
- Supports hybrid workforce security
Cons
- Enterprise-focused pricing
- Setup requires IT resources
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SSO, MFA, encryption, audit logs
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- IAM, endpoint security, SIEM
Support & Community
Professional support and services
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Zscaler Private Access | Enterprise hybrid workforce | Web | Cloud | Cloud-native scalable ZTNA | N/A |
| Palo Alto Prisma Access | Enterprise with threat prevention | Web | Cloud | Integrated threat protection | N/A |
| Netskope Private Access | SaaS + private apps | Web | Cloud | Adaptive policies | N/A |
| Akamai EAA | Application segmentation | Web | Cloud | Granular application-level access | N/A |
| Cloudflare Access | SMB & enterprise apps | Web | Cloud | Identity-based access | N/A |
| Microsoft Azure AD App Proxy | Microsoft-centric environments | Web | Cloud | Conditional access & SSO | N/A |
| Symantec Secure Access Cloud | Enterprise ZTNA | Web | Cloud | Least-privilege enforcement | N/A |
| Cato Networks Cloud ZTNA | SD-WAN + security | Web | Cloud | Unified network & ZTNA | N/A |
| Netskope NPA | Private & SaaS apps | Web | Cloud | Context-aware policies | N/A |
| Ivanti ZTNA | Hybrid workforce access | Web | Cloud | Continuous risk evaluation | N/A |
Evaluation & Scoring of Zero Trust Network Access (ZTNA)
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Zscaler Private Access | 9 | 7 | 8 | 9 | 9 | 8 | 7 | 8.4 |
| Prisma Access | 9 | 6 | 9 | 9 | 9 | 8 | 7 | 8.3 |
| Netskope Private Access | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.8 |
| Akamai EAA | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.7 |
| Cloudflare Access | 7 | 9 | 6 | 8 | 8 | 8 | 8 | 8.0 |
| Azure AD App Proxy | 7 | 8 | 7 | 8 | 7 | 8 | 8 | 7.7 |
| Symantec Secure Access Cloud | 8 | 6 | 8 | 8 | 8 | 7 | 7 | 7.8 |
| Cato Networks Cloud ZTNA | 8 | 6 | 8 | 8 | 8 | 7 | 7 | 7.8 |
| Netskope NPA | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.7 |
| Ivanti ZTNA | 7 | 7 | 7 | 8 | 7 | 7 | 7 | 7.5 |
Scores provide a comparative assessment across core features, usability, integrations, security, performance, support, and value.
Which Zero Trust Network Access (ZTNA) Tool Is Right for You?
Solo / Freelancer
ZTNA may not be necessary for individual users or very small teams. Lightweight identity management may suffice.
SMB
Cloudflare Access and Azure AD App Proxy provide simple, cost-effective solutions for small or mid-sized organizations.
Mid-Market
Netskope Private Access and Ivanti ZTNA balance scalability, adaptive policies, and monitoring for growing enterprises.
Enterprise
Zscaler Private Access and Palo Alto Prisma Access are ideal for global organizations requiring enterprise-grade ZTNA with robust analytics and security.
Budget vs Premium
Cloudflare and Azure AD App Proxy are cost-efficient; ZPA and Prisma Access deliver premium, enterprise capabilities.
Feature Depth vs Ease of Use
Cloudflare Access prioritizes usability; ZPA and Prisma Access offer deeper policy and integration capabilities.
Integrations & Scalability
Enterprises should prioritize Zscaler, Prisma Access, and Netskope for extensive IAM, SIEM, and SASE integrations.
Security & Compliance Needs
Enterprises requiring strict auditability, encryption, and regulatory compliance should select solutions with SOC 2, ISO 27001, and GDPR coverage.
Frequently Asked Questions (FAQs)
1. What pricing models do ZTNA solutions use?
Most vendors offer subscription-based pricing by user or seat, with enterprise plans negotiated based on scale and features.
2. How long does deployment take?
Cloud-native ZTNA can deploy within days for SMBs; enterprise deployments with IAM and SIEM integrations may take weeks.
3. Can ZTNA replace VPNs?
Yes, ZTNA is designed to replace VPNs for secure, application-level access without network exposure.
4. Do ZTNA tools support remote and hybrid work?
Yes, they are specifically designed for distributed workforces, providing secure access from any location.
5. Are ZTNA solutions compatible with existing IAM?
Most integrate with SSO, MFA, and IAM providers to enforce identity-centric access controls.
6. How is device posture evaluated?
ZTNA platforms check endpoint compliance, configuration, and security before granting access.
7. Can ZTNA secure SaaS applications?
Yes, many solutions extend zero trust policies to SaaS, private cloud, and legacy apps.
8. Are logs available for compliance audits?
ZTNA platforms provide logging and reporting for audit purposes and integration with SIEM.
9. Do ZTNA solutions support BYOD?
Yes, conditional access and posture verification enforce security on personal devices.
10. How should organizations select a ZTNA tool?
Consider deployment complexity, integrations, scale, and policy enforcement capabilities. Pilot shortlisted solutions for evaluation.
Conclusion
Zero Trust Network Access is a critical component of modern cybersecurity, providing least-privilege access and continuous verification across hybrid workforces and cloud environments. Organizations seeking cost-efficient solutions can consider Cloudflare Access or Azure AD App Proxy, while mid-market enterprises benefit from Netskope Private Access and Ivanti ZTNA. Large global enterprises should evaluate Zscaler Private Access and Palo Alto Prisma Access for enterprise-grade security, analytics, and scalability. Selecting a ZTNA solution requires careful consideration of integrations, usability, policy management, and security compliance. Organizations should shortlist candidates, run pilots, and validate access policies to ensure secure, compliant, and efficient access control.
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals