Introduction
Identity Governance & Administration (IGA) is a comprehensive framework that allows organizations to manage digital identities, enforce access policies, and ensure compliance across systems. Unlike traditional identity management, IGA focuses not only on provisioning accounts but also on auditing, role-based access controls, and lifecycle management of user identities.
In as businesses increasingly rely on cloud platforms, SaaS applications, and hybrid IT environments, IGA has become essential for maintaining security, ensuring regulatory compliance, and managing operational efficiency. Organizations face the challenge of granting the right access to the right users while minimizing risk, and IGA tools provide a structured approach to achieve this balance.Real-world use cases include automated onboarding/offboarding, ensuring least-privilege access, enforcing access certifications, managing privileged accounts, and auditing user activities for compliance purposes.
When evaluating IGA tools, buyers should assess features such as automated provisioning, access request workflows, policy enforcement, auditing and reporting, integration with IAM/SSO/MFA, role management, scalability, cloud support, and compliance certifications.
Best for: IT security teams, compliance officers, enterprises of all sizes, organizations subject to regulations such as GDPR, HIPAA, and SOC 2.
Not ideal for: Small organizations with minimal access control needs or low compliance requirements; simpler identity management solutions may suffice.
Key Trends in Identity Governance & Administration (IGA)
- Integration with AI/ML for access risk analysis and anomaly detection
- Automation of user provisioning and de-provisioning workflows
- Support for zero-trust security frameworks
- Enhanced auditing and compliance reporting capabilities
- Unified integration with IAM, SSO, and MFA solutions
- Cloud-first and hybrid deployment models
- Role-based and attribute-based access control
- Adaptive and risk-based access policies
- API-first and extensible platforms for enterprise integration
- Flexible subscription and usage-based pricing models
How We Selected These Tools (Methodology)
- Evaluated market adoption and brand recognition
- Assessed feature completeness for provisioning, access certification, and auditing
- Reviewed reliability and performance signals
- Verified security posture and compliance certifications
- Checked integrations with IAM, SSO, MFA, and SIEM systems
- Examined scalability and customer fit across enterprise segments
- Considered automation capabilities for access requests and approvals
- Evaluated reporting, analytics, and compliance tools
- Assessed deployment flexibility: cloud, on-premises, hybrid
- Considered total cost of ownership and enterprise ROI
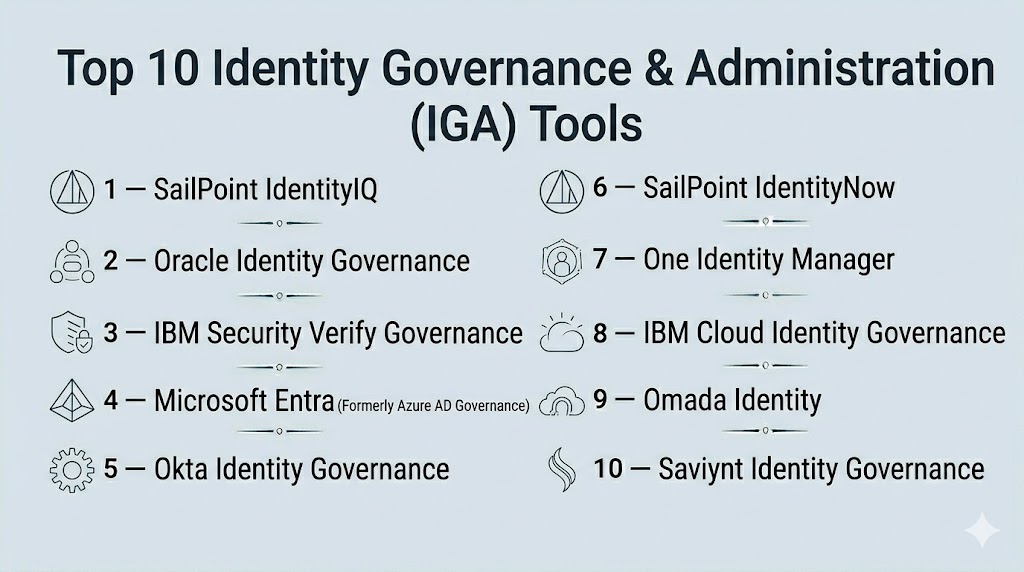
Top 10 Identity Governance & Administration (IGA) Tools
#1 — SailPoint IdentityIQ
Short description : SailPoint IdentityIQ offers a comprehensive IGA solution for enterprise environments, enabling automated identity lifecycle management, access governance, and compliance reporting.
Key Features
- Automated provisioning and de-provisioning
- Role-based access control and certifications
- Access request and approval workflows
- Policy enforcement and audit reporting
- Integration with IAM, SSO, and MFA systems
Pros
- Scalable for large enterprises
- Robust compliance and reporting tools
- Strong automation capabilities
Cons
- High implementation complexity
- Premium pricing
Platforms / Deployment
- Web / Windows / Linux
- Cloud / On-premises / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Extensive connectors for cloud apps and enterprise systems
- API access for custom integrations
- Supports SSO and MFA
Support & Community
- 24/7 enterprise support, training programs, knowledge base
#2 — Oracle Identity Governance
Short description : Oracle Identity Governance provides end-to-end IGA with automated provisioning, risk-based access management, and compliance controls for global enterprises.
Key Features
- Automated user lifecycle management
- Role and entitlement management
- Access certification and audit reporting
- Policy-based governance
- Integration with SSO, MFA, and cloud applications
Pros
- Enterprise-grade scalability
- Strong compliance capabilities
- Advanced policy management
Cons
- Complex deployment
- Higher learning curve
Platforms / Deployment
- Web / Windows / Linux
- Cloud / On-premises / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR, HIPAA
Integrations & Ecosystem
- Integrates with IAM, SIEM, and cloud services
- API extensibility
- Supports enterprise SSO
Support & Community
- Enterprise support, documentation, professional services
#3 — IBM Security Verify Governance
Short description : IBM Security Verify Governance enables automated identity lifecycle management, policy enforcement, and risk-based access governance for enterprises.
Key Features
- Automated provisioning and de-provisioning
- Role and access management
- Access certification workflows
- Audit and compliance reporting
- Integration with IAM and SSO solutions
Pros
- Strong analytics and reporting
- Scalable for large enterprises
- Supports cloud and hybrid environments
Cons
- Complex interface for new users
- Premium cost
Platforms / Deployment
- Web / Windows / Linux
- Cloud / Hybrid / On-premises
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- IAM and SSO integration
- SIEM connectors
- REST APIs for custom extensions
Support & Community
- Enterprise-level support, training, knowledge base
#4 — Microsoft Entra (Formerly Azure AD Governance)
Short description : Microsoft Entra provides IGA features integrated with Azure AD for lifecycle management, access reviews, and policy enforcement across Microsoft and third-party applications.
Key Features
- Identity lifecycle automation
- Access review and certification
- Role-based access policies
- Policy enforcement for cloud and on-prem apps
- Integration with Microsoft ecosystem
Pros
- Native integration with Microsoft products
- Cloud-native and scalable
- Simplified interface for admins
Cons
- Limited non-Microsoft integrations
- Advanced features may require premium licensing
Platforms / Deployment
- Web / Windows / Cloud-based
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Deep Microsoft 365 integration
- API access for third-party apps
- Supports MFA and SSO
Support & Community
- Microsoft support, documentation, and community forums
#5 — Okta Identity Governance
Short description : Okta Identity Governance automates user lifecycle management, role-based access control, and compliance reporting for cloud-first enterprises.
Key Features
- Automated provisioning and de-provisioning
- Access requests and approvals
- Policy-based governance
- Access certifications and auditing
- Integration with SSO, MFA, and cloud apps
Pros
- Cloud-native and easy to deploy
- Strong analytics and reporting
- Supports hybrid environments
Cons
- Some advanced features limited to enterprise plans
- May require additional integrations for complex setups
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SOC 2, ISO 27001, GDPR, HIPAA
Integrations & Ecosystem
- Cloud SaaS connectors
- API extensibility
- IAM and SSO integration
Support & Community
- 24/7 support, knowledge base, community forums
#6 — SailPoint IdentityNow
Short description : SailPoint IdentityNow is a cloud-based IGA platform enabling automated identity lifecycle management, compliance, and access governance.
Key Features
- Cloud-first provisioning and de-provisioning
- Access requests and approvals
- Policy and role management
- Audit and compliance reporting
- Integration with cloud SaaS apps
Pros
- Quick cloud deployment
- Scalable and secure
- AI-driven access insights
Cons
- Limited on-premises functionality
- Premium licensing
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- SaaS connectors
- API access for custom integration
- SSO and MFA support
Support & Community
- Enterprise support, training, and documentation
#7 — One Identity Manager
Short description : One Identity Manager streamlines identity governance with role-based access control, lifecycle automation, and compliance reporting for enterprises.
Key Features
- User provisioning and de-provisioning
- Role and entitlement management
- Policy enforcement and auditing
- Access certification workflows
- Integration with IAM and SSO systems
Pros
- Comprehensive enterprise functionality
- Strong compliance features
- Supports hybrid and cloud environments
Cons
- Implementation complexity
- Requires administrative training
Platforms / Deployment
- Web / Windows / Linux
- Cloud / Hybrid / On-premises
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- IAM and SSO connectors
- API access
- Integration with SIEM
Support & Community
- Enterprise support, professional services, documentation
#8 — IBM Cloud Identity Governance
Short description : IBM Cloud Identity Governance provides cloud-native IGA capabilities including automated provisioning, access certification, and compliance reporting.
Key Features
- Automated user lifecycle management
- Access certification and review
- Policy enforcement and auditing
- Role-based access controls
- Integration with cloud applications
Pros
- Cloud-first and scalable
- Supports hybrid environments
- Robust analytics
Cons
- Limited on-premises capabilities
- Premium pricing
Platforms / Deployment
- Web / Cloud
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- SaaS connectors
- IAM integration
- API access
Support & Community
- Enterprise support, knowledge base, training
#9 — Omada Identity
Short description : Omada Identity enables enterprises to manage user identities, enforce access policies, and maintain compliance through automated workflows.
Key Features
- Automated provisioning and de-provisioning
- Access request and approval workflows
- Policy enforcement and role management
- Compliance reporting and auditing
- Integration with IAM and SSO
Pros
- Scalable for mid-market and enterprise
- Strong compliance reporting
- Flexible deployment
Cons
- May require additional integrations
- Learning curve for complex environments
Platforms / Deployment
- Web / Windows / Linux
- Cloud / Hybrid / On-premises
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- IAM and SSO connectors
- API extensibility
- SIEM integration
Support & Community
- Documentation, support tiers, professional services
#10 — Saviynt Identity Governance
Short description : Saviynt provides cloud-based IGA with identity lifecycle automation, risk-based access governance, and compliance reporting for large enterprises.
Key Features
- Automated provisioning and de-provisioning
- Risk-based access policies
- Access certification and auditing
- Policy enforcement
- Integration with IAM, SSO, and cloud apps
Pros
- Cloud-native and scalable
- Strong risk analytics
- Supports hybrid environments
Cons
- Premium pricing
- Implementation complexity
Platforms / Deployment
- Web / Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR, HIPAA
Integrations & Ecosystem
- Cloud connectors
- API and SSO integration
- IAM and SIEM connectors
Support & Community
- Enterprise support, training, and documentation
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| SailPoint IdentityIQ | Enterprise | Web, Windows, Linux | Cloud/On-prem | Comprehensive governance | N/A |
| Oracle Identity Governance | Enterprise | Web, Windows, Linux | Cloud/Hybrid | Risk-based access | N/A |
| IBM Security Verify Governance | Enterprise | Web, Windows, Linux | Cloud/Hybrid | Access analytics | N/A |
| Microsoft Entra | Enterprise | Web | Cloud | Azure-native IGA | N/A |
| Okta Identity Governance | Cloud-first | Web | Cloud | Cloud-native automation | N/A |
| SailPoint IdentityNow | Cloud-first | Web | Cloud | AI-driven insights | N/A |
| One Identity Manager | Enterprise | Web, Windows, Linux | Cloud/Hybrid/On-prem | Lifecycle automation | N/A |
| IBM Cloud Identity Governance | Cloud-first | Web | Cloud | Cloud-native governance | N/A |
| Omada Identity | Enterprise | Web, Windows, Linux | Cloud/Hybrid | Compliance automation | N/A |
| Saviynt Identity Governance | Enterprise | Web | Cloud/Hybrid | Risk-based governance | N/A |
Evaluation & Scoring of Identity Governance & Administration (IGA)
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| SailPoint IdentityIQ | 10 | 8 | 9 | 9 | 9 | 9 | 8 | 9.0 |
| Oracle Identity Governance | 9 | 7 | 9 | 9 | 8 | 8 | 7 | 8.3 |
| IBM Security Verify Governance | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.2 |
| Microsoft Entra | 8 | 9 | 7 | 8 | 8 | 8 | 8 | 8.1 |
| Okta Identity Governance | 9 | 8 | 8 | 8 | 8 | 8 | 7 | 8.1 |
| SailPoint IdentityNow | 9 | 8 | 8 | 8 | 8 | 8 | 7 | 8.0 |
| One Identity Manager | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.8 |
| IBM Cloud Identity Governance | 8 | 8 | 7 | 8 | 8 | 8 | 7 | 7.8 |
| Omada Identity | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.5 |
| Saviynt Identity Governance | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.5 |
Interpretation: Weighted totals reflect the balance of core features, ease of use, security, integrations, and value for enterprises and mid-market organizations.
Which Identity Governance & Administration (IGA) Tool Is Right for You?
Solo / Freelancer
IGA platforms are generally unnecessary; lightweight IAM or identity tools suffice.
SMB
Okta Identity Governance, Omada Identity, and SailPoint IdentityNow provide cloud-based, affordable solutions for mid-market needs.
Mid-Market
SailPoint IdentityNow, One Identity Manager, and Saviynt support hybrid deployments and advanced compliance.
Enterprise
SailPoint IdentityIQ, Oracle Identity Governance, IBM Security Verify Governance, and Microsoft Entra deliver comprehensive governance, automation, and regulatory compliance.
Budget vs Premium
Mid-market may prioritize cloud-first, simpler solutions, while enterprises benefit from full-featured platforms.
Feature Depth vs Ease of Use
Enterprise-focused tools provide granular control, compliance, and automation; mid-market tools prioritize usability.
Integrations & Scalability
Cloud and hybrid platforms allow seamless integration with IAM, SSO, MFA, and SIEM for scalable identity management.
Security & Compliance Needs
Tools with SOC 2, ISO 27001, GDPR, and HIPAA certifications provide assurance for regulated industries.
Frequently Asked Questions (FAQs)
1. What is the difference between IAM and IGA?
IAM focuses on access control and authentication, while IGA adds governance, auditing, and policy enforcement for compliance and risk management.
2. Can IGA integrate with SSO and MFA?
Yes, modern IGA platforms integrate with SSO and MFA for enhanced access security.
3. Are IGA tools cloud-based or on-premises?
Most vendors offer both cloud and hybrid deployment models to accommodate enterprise needs.
4. How does IGA help with compliance?
IGA provides audit trails, access certification, and policy enforcement to support regulations such as GDPR, HIPAA, and SOC 2.
5. Can IGA automate user provisioning?
Yes, IGA automates onboarding, offboarding, and role-based access assignment.
6. Does IGA support role-based access control?
Yes, role-based and attribute-based access control are core IGA functionalities.
7. Is IGA scalable for large enterprises?
Yes, enterprise-grade IGA platforms support thousands of users and applications across hybrid environments.
8. Can IGA manage third-party vendor access?
Yes, many IGA platforms include workflows for temporary and controlled access for contractors and partners.
9. How do IGA tools integrate with existing IT infrastructure?
Via connectors, APIs, and integrations with IAM, SSO, MFA, and SIEM solutions.
10. What are common challenges in implementing IGA?
Complex deployment, integration with legacy systems, and ensuring accurate role and entitlement definitions.
Conclusion
Identity Governance & Administration is critical for managing digital identities, enforcing access policies, and maintaining compliance across enterprise IT environments. Mid-market organizations can leverage cloud-based solutions such as Okta Identity Governance and SailPoint IdentityNow, while large enterprises benefit from comprehensive platforms like SailPoint IdentityIQ, Oracle Identity Governance, and IBM Security Verify Governance. Organizations should evaluate these tools based on deployment needs, integration capabilities, compliance requirements, and scalability. Pilot testing and robust implementation planning help ensure effective identity governance across the enterprise.
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals