Introduction
Security Information and Event Management (SIEM) platforms are a central pillar of modern cybersecurity operations. They aggregate log data from across an organization’s IT environment, normalize it, and analyze it to detect threats, anomalies, and compliance violations. SIEM systems combine real-time monitoring with historical analysis to provide a holistic view of security events, enabling faster incident detection and response.In organizations face increasingly sophisticated cyber threats, from ransomware attacks to insider threats and supply chain attacks. SIEM tools help businesses address these challenges by correlating events, providing actionable alerts, and supporting compliance with regulations such as GDPR, HIPAA, and SOC 2. Use cases include detecting unauthorized access, monitoring privileged accounts, identifying suspicious network traffic, automating threat response, and generating audit-ready compliance reports.
When evaluating SIEM solutions, buyers should consider factors like deployment flexibility, data ingestion and normalization capabilities, real-time alerting, threat intelligence integration, automation and orchestration, scalability, reporting and compliance, ease of use, performance, and total cost of ownership.
Best for: Security operations centers (SOCs), enterprise IT security teams, organizations handling sensitive or regulated data, multi-site or hybrid IT environments.
Not ideal for: Small businesses with minimal IT infrastructure or low risk profiles, where simpler log management or endpoint security solutions may suffice.
Key Trends in Security Information & Event Management (SIEM)
- AI and machine learning for predictive threat detection
- Automation of alert triage and incident response
- Cloud-native and hybrid deployment models
- Integration with Extended Detection & Response (XDR) platforms
- Enhanced compliance reporting and regulatory support
- Threat intelligence and third-party data integration
- Support for IoT, OT, and hybrid network environments
- Adaptive alerting with risk-based prioritization
- Managed SIEM and Security-as-a-Service models
- Subscription-based pricing for scalable deployment
How We Selected These Tools (Methodology)
- Market adoption and vendor mindshare
- Feature completeness for event collection, correlation, and response
- Reliability and performance in large-scale environments
- Security posture and compliance support
- Integration with existing security infrastructure and ecosystems
- Automation and orchestration capabilities
- Deployment flexibility (on-prem, cloud, hybrid)
- Reporting and analytics capabilities
- Customer feedback and support services
- Cost-effectiveness and pricing transparency
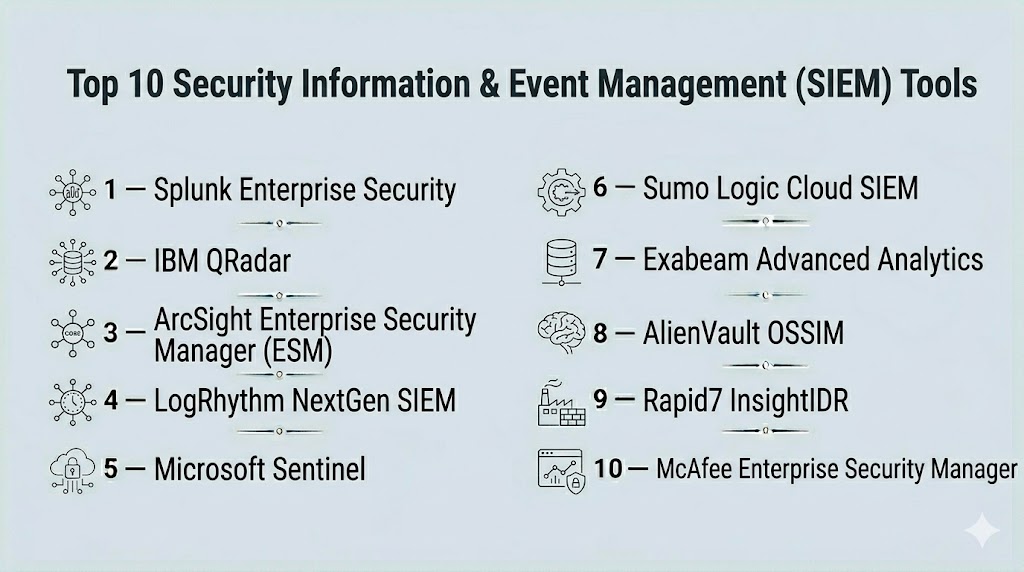
Top 10 Security Information & Event Management (SIEM) Tools
#1 — Splunk Enterprise Security
Short description : Splunk Enterprise Security provides advanced analytics, log management, and threat intelligence for real-time threat detection and response. Ideal for large enterprises requiring deep visibility into complex IT environments.
Key Features
- Real-time event correlation and alerting
- AI-driven anomaly detection
- Threat intelligence integration
- Compliance and audit reporting
- Custom dashboards and analytics
- Automation and workflow orchestration
- Cloud and hybrid deployment support
Pros
- Highly scalable and flexible
- Strong analytics and visualization capabilities
- Extensive third-party integrations
Cons
- High cost for large deployments
- Steeper learning curve for complex use
Platforms / Deployment
- Web / Windows / Linux
- Cloud / On-prem / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR
- MFA, encryption, RBAC
Integrations & Ecosystem
- Threat intelligence feeds
- SOAR platforms
- APIs for custom integrations
Support & Community
- Enterprise support, extensive documentation, active user community
#2 — IBM QRadar
Short description : IBM QRadar consolidates log management, threat detection, and compliance reporting with AI-assisted analytics, supporting rapid threat response across enterprise networks.
Key Features
- Event and flow data correlation
- AI-powered anomaly detection
- Real-time dashboards
- Compliance and reporting templates
- Integration with threat intelligence
- Automated alert prioritization
Pros
- Strong correlation capabilities
- Supports large-scale enterprise environments
- Comprehensive compliance support
Cons
- Complex deployment and configuration
- Licensing may be expensive
Platforms / Deployment
- Web / Windows / Linux
- Cloud / On-prem / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR, HIPAA
Integrations & Ecosystem
- SIEM/XDR platforms
- APIs and custom integrations
- Threat intelligence sources
Support & Community
- Enterprise support, onboarding, active forums
#3 — ArcSight Enterprise Security Manager (ESM)
Short description : ArcSight ESM provides real-time event correlation, threat detection, and compliance reporting with a focus on enterprise security operations.
Key Features
- Real-time log aggregation and analysis
- Threat correlation and anomaly detection
- Compliance reporting and audit trails
- Integration with SIEM ecosystem
- Customizable dashboards and alerts
Pros
- Scalable for large enterprises
- Strong threat correlation capabilities
- Supports regulatory compliance
Cons
- Complex interface for new users
- Requires ongoing tuning for optimal results
Platforms / Deployment
- Web / Windows / Linux
- On-prem / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Threat intelligence feeds
- SOAR and XDR platforms
- APIs for workflow automation
Support & Community
- Enterprise support, documentation, user community
#4 — LogRhythm NextGen SIEM
Short description : LogRhythm offers centralized logging, AI-driven threat detection, and automated response, designed for enterprise SOCs and compliance-driven environments.
Key Features
- Advanced log management
- AI/ML-powered threat detection
- Automated incident response
- Compliance reporting
- Threat intelligence integration
Pros
- Comprehensive SOC platform
- Intuitive dashboards
- Efficient incident response workflows
Cons
- Can be resource-intensive
- Learning curve for advanced features
Platforms / Deployment
- Web / Windows / Linux
- Cloud / On-prem / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- APIs for automation
- SOAR and threat intelligence feeds
- Cloud integrations
Support & Community
- 24/7 support, documentation, user forums
#5 — Microsoft Sentinel
Short description : Microsoft Sentinel is a cloud-native SIEM providing intelligent security analytics, threat detection, and incident response across enterprise cloud and hybrid environments.
Key Features
- Cloud-native log collection and analytics
- AI-driven anomaly detection
- Automated playbooks for response
- Integration with Microsoft 365 and Azure
- Compliance reporting templates
Pros
- Easy cloud deployment
- Integrates well with Microsoft ecosystem
- Scalable and flexible
Cons
- Cloud-only may not suit on-prem-heavy environments
- Licensing costs for large-scale use
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SOC 2, ISO 27001, GDPR, HIPAA
Integrations & Ecosystem
- Microsoft ecosystem
- APIs and connectors
- SOAR tools
Support & Community
- Microsoft enterprise support, documentation, active forums
#6 — Sumo Logic Cloud SIEM
Short description : Sumo Logic provides a cloud-native SIEM with log aggregation, threat detection, and AI-assisted analytics for hybrid and cloud-first enterprises.
Key Features
- Real-time log and metrics monitoring
- AI-driven threat detection
- Compliance dashboards
- Automated alerting
- Cloud-native scalability
Pros
- Cloud-native and highly scalable
- Integrated AI analytics
- Fast deployment
Cons
- Limited on-prem capabilities
- May require advanced tuning for complex networks
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Cloud connectors
- APIs for automation
- Threat intelligence feeds
Support & Community
- 24/7 support, documentation, user forums
#7 — Exabeam Advanced Analytics
Short description : Exabeam leverages user and entity behavior analytics (UEBA) to detect threats and automate responses, integrated with SIEM for comprehensive visibility.
Key Features
- UEBA-powered threat detection
- Automated incident response workflows
- Behavior modeling for users and devices
- Threat intelligence integration
- Compliance reporting
Pros
- Strong behavioral analytics
- Effective at insider threat detection
- Integrates with multiple SIEMs
Cons
- Premium pricing
- Requires configuration for optimal results
Platforms / Deployment
- Web / Windows / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- SIEM platforms
- APIs for automation
- Threat intelligence
Support & Community
- Enterprise support, documentation, online community
#8 — AlienVault OSSIM
Short description : AlienVault OSSIM is an open-source SIEM providing basic log management, threat detection, and compliance monitoring for smaller organizations or labs.
Key Features
- Log aggregation and correlation
- Threat intelligence integration
- Basic alerting and dashboards
- Compliance reporting
- Open-source extensibility
Pros
- Free and open-source
- Easy to experiment and learn SIEM fundamentals
- Integrates with many plugins
Cons
- Limited scalability for large enterprises
- Lacks advanced analytics and automation
Platforms / Deployment
- Windows / Linux
- On-prem / Hybrid
Security & Compliance
- Varies / N/A
Integrations & Ecosystem
- Open-source plugins
- APIs for custom integrations
- Threat intelligence feeds
Support & Community
- Community support, forums, documentation
#9 — Rapid7 InsightIDR
Short description : InsightIDR combines SIEM, UEBA, and endpoint detection for proactive threat detection and incident response in enterprise networks.
Key Features
- Real-time log collection
- UEBA threat detection
- Automated alerting and playbooks
- Endpoint and network visibility
- Compliance dashboards
Pros
- Integrated endpoint and network visibility
- User-friendly dashboards
- Automation reduces manual response
Cons
- Cloud-first may limit on-prem flexibility
- Licensing scales with endpoints
Platforms / Deployment
- Web / Windows / Linux
- Cloud / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- APIs for automation
- SOAR and threat intelligence integrations
- Cloud connectors
Support & Community
- 24/7 support, documentation, forums
#10 — McAfee Enterprise Security Manager
Short description : McAfee ESM provides centralized SIEM functionality, combining event correlation, advanced analytics, and compliance reporting for enterprise environments.
Key Features
- Real-time event correlation
- Threat intelligence integration
- Compliance dashboards
- Automated alerting
- Scalable architecture
Pros
- Mature platform with enterprise-grade features
- Strong integration with McAfee ecosystem
- Scalable and reliable
Cons
- Complex deployment
- Higher licensing costs
Platforms / Deployment
- Web / Windows / Linux
- On-prem / Hybrid
Security & Compliance
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- McAfee products
- SIEM/XDR platforms
- API integration
Support & Community
- Enterprise support, documentation, community forums
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Splunk Enterprise Security | Enterprise | Web, Windows, Linux | Cloud/On-prem/Hybrid | AI-driven analytics | N/A |
| IBM QRadar | Enterprise | Web, Windows, Linux | Cloud/On-prem/Hybrid | Correlation & threat intelligence | N/A |
| ArcSight ESM | Enterprise | Web, Windows, Linux | On-prem/Hybrid | Real-time event correlation | N/A |
| LogRhythm | Enterprise | Web, Windows, Linux | Cloud/On-prem/Hybrid | AI/ML analytics | N/A |
| Microsoft Sentinel | Enterprise | Web | Cloud | Cloud-native analytics | N/A |
| Sumo Logic | Cloud/SaaS | Web | Cloud | Cloud-native SIEM | N/A |
| Exabeam | Enterprise | Web, Windows, Linux | Cloud/Hybrid | UEBA behavioral analytics | N/A |
| AlienVault OSSIM | SMB/Lab | Windows, Linux | On-prem/Hybrid | Open-source SIEM | N/A |
| Rapid7 InsightIDR | Mid-Market | Web, Windows, Linux | Cloud/Hybrid | UEBA + endpoint visibility | N/A |
| McAfee ESM | Enterprise | Web, Windows, Linux | On-prem/Hybrid | Enterprise-grade analytics | N/A |
Evaluation & Scoring of Security Information & Event Management (SIEM)
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Splunk Enterprise Security | 10 | 9 | 9 | 9 | 9 | 9 | 8 | 9.0 |
| IBM QRadar | 9 | 8 | 8 | 9 | 8 | 8 | 8 | 8.3 |
| ArcSight ESM | 9 | 8 | 8 | 8 | 8 | 8 | 7 | 8.0 |
| LogRhythm | 9 | 8 | 8 | 8 | 8 | 8 | 7 | 7.9 |
| Microsoft Sentinel | 8 | 9 | 8 | 8 | 8 | 8 | 8 | 8.2 |
| Sumo Logic | 8 | 8 | 8 | 8 | 8 | 8 | 7 | 7.8 |
| Exabeam | 9 | 8 | 8 | 9 | 8 | 8 | 7 | 8.0 |
| AlienVault OSSIM | 7 | 7 | 7 | 7 | 7 | 7 | 7 | 7.0 |
| Rapid7 InsightIDR | 9 | 8 | 8 | 9 | 8 | 8 | 7 | 8.0 |
| McAfee ESM | 9 | 8 | 8 | 8 | 8 | 8 | 7 | 7.9 |
Interpretation: Scores provide a comparative view of how each SIEM balances core detection features, integrations, usability, and value for enterprise and mid-market deployments.
Which Security Information & Event Management (SIEM) Tool Is Right for You?
Solo / Freelancer
Simpler log management tools or open-source SIEMs like AlienVault OSSIM may suffice for small networks or personal labs.
SMB
Mid-market organizations can leverage Rapid7 InsightIDR or Sumo Logic for cloud-native, manageable SIEM solutions.
Mid-Market
Microsoft Sentinel and LogRhythm provide robust analytics and automated response capabilities suitable for growing enterprises.
Enterprise
Large-scale enterprises benefit from Splunk Enterprise Security, IBM QRadar, ArcSight ESM, and McAfee ESM for comprehensive event correlation, AI analytics, and compliance management.
Budget vs Premium
Open-source or cloud-native tools reduce upfront costs, whereas premium enterprise solutions offer deeper analytics, integrations, and support.
Feature Depth vs Ease of Use
Enterprise SIEMs offer extensive features but require dedicated teams; cloud-native tools provide simpler deployment and management.
Integrations & Scalability
Integrations with XDR, SOAR, and threat intelligence platforms enhance detection and response capabilities across hybrid networks.
Security & Compliance Needs
Organizations in regulated sectors must prioritize SIEMs that provide compliance reporting, audit trails, and integration with existing security frameworks.
Frequently Asked Questions (FAQs)
1. What is a SIEM platform?
A SIEM platform aggregates log and event data from across an organization to detect threats, anomalies, and compliance violations in real time.
2. How does SIEM differ from NDR?
SIEM focuses on event correlation and log management, while NDR specializes in real-time network traffic analysis and behavioral threat detection.
3. Are cloud-native SIEMs effective?
Yes, cloud-native SIEMs offer scalability, faster deployment, and easier integration with cloud infrastructure compared to traditional on-prem solutions.
4. Can SIEM detect insider threats?
Yes, through user and entity behavior analytics, SIEM platforms can identify unusual actions that may indicate insider threats.
5. How do SIEM platforms integrate with SOAR tools?
SIEMs provide alerts and log data that SOAR tools use to automate responses and orchestrate workflows for incident management.
6. Are SIEM platforms suitable for small businesses?
Yes, but small businesses may prefer cloud-native or open-source SIEMs due to lower complexity and cost.
7. What industries benefit most from SIEM?
Finance, healthcare, government, critical infrastructure, and large enterprises with complex IT environments benefit most.
8. How does SIEM support compliance?
SIEM platforms generate audit trails, compliance reports, and dashboards aligned with GDPR, HIPAA, SOC 2, and other regulations.
9. Can SIEM detect zero-day attacks?
Yes, advanced SIEMs with AI/ML analytics can detect anomalous behavior indicative of zero-day attacks.
10. How long does deployment take?
Deployment varies by scale and complexity, ranging from a few weeks for cloud-native solutions to several months for enterprise on-prem installations.
Conclusion
Security Information & Event Management (SIEM) platforms remain essential for organizations aiming to centralize threat detection, enhance security visibility, and maintain compliance. Choosing the right SIEM depends on network complexity, deployment preference, threat exposure, and regulatory requirements. Cloud-native options like Microsoft Sentinel and Sumo Logic offer scalability and ease of use, while enterprise solutions such as Splunk Enterprise Security, IBM QRadar, and ArcSight ESM provide advanced analytics and integrations. Organizations should shortlist tools based on deployment needs, test pilot implementations, and validate integration capabilities with existing SOC and XDR infrastructures to ensure effective threat management.
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals