Introduction
Attack Surface Management (ASM) tools help organizations identify, monitor, and manage their exposed digital assets to reduce cyber risk. They provide visibility into all publicly accessible systems, applications, and services, including cloud workloads, web applications, APIs, and third-party integrations. By continuously scanning for vulnerabilities, misconfigurations, and unknown assets, ASM tools allow security teams to proactively reduce the potential entry points for attackers.
In , with hybrid cloud adoption, remote work, and complex IT ecosystems, ASM is essential for organizations to maintain a real-time understanding of their attack surface. These tools not only improve cybersecurity posture but also aid in compliance with regulatory standards such as GDPR, HIPAA, and ISO 27001.
Real-world use cases include:
- Discovering unknown or shadow IT assets exposed to the internet.
- Prioritizing vulnerabilities based on risk and exploitability.
- Continuous monitoring of cloud environments for misconfigurations.
- Identifying exposed APIs and sensitive data leaks.
- Supporting penetration testing and red team exercises.
Evaluation criteria for buyers often include:
- Asset discovery coverage and accuracy
- Continuous monitoring and alerting
- Risk-based vulnerability prioritization
- Integration with SIEM, SOAR, and ITSM tools
- Cloud, on-premises, and hybrid support
- Automation and remediation capabilities
- Reporting and analytics dashboards
- Scalability for large organizations
- Pricing model and licensing flexibility
- Security and compliance support
Best for: Security teams, IT managers, risk officers, and enterprises needing visibility into complex digital footprints. Ideal for industries like finance, healthcare, and critical infrastructure.
Not ideal for: Very small organizations with minimal digital assets, or teams without cybersecurity expertise where simpler vulnerability scanning may suffice.
Key Trends in Attack Surface Management (ASM)
- AI-driven discovery and prioritization of assets and vulnerabilities.
- Integration with threat intelligence feeds for proactive risk reduction.
- Continuous scanning of cloud and SaaS environments.
- Automation of alerts and remediation workflows.
- Support for hybrid and multi-cloud ecosystems.
- Risk scoring and prioritization for exposed assets.
- Self-service dashboards for security and DevOps teams.
- Subscription-based and usage-based pricing models.
- Interoperability with SIEM, SOAR, and vulnerability management platforms.
- Enhanced compliance reporting for GDPR, HIPAA, and industry-specific standards.
How We Selected These Tools (Methodology)
- Assessed market adoption and industry mindshare across enterprises.
- Evaluated feature completeness, including discovery, monitoring, and analytics.
- Reviewed performance and reliability for large-scale environments.
- Verified security posture and compliance support (GDPR, HIPAA, ISO 27001).
- Analyzed integration capabilities with SIEM, SOAR, and ITSM platforms.
- Considered customer fit across SMB, mid-market, and enterprise organizations.
- Balanced commercial and emerging solutions for diversity.
- Reviewed usability, onboarding, and reporting capabilities.
- Checked vendor support, documentation, and community engagement.
- Assessed licensing flexibility and cost-effectiveness.
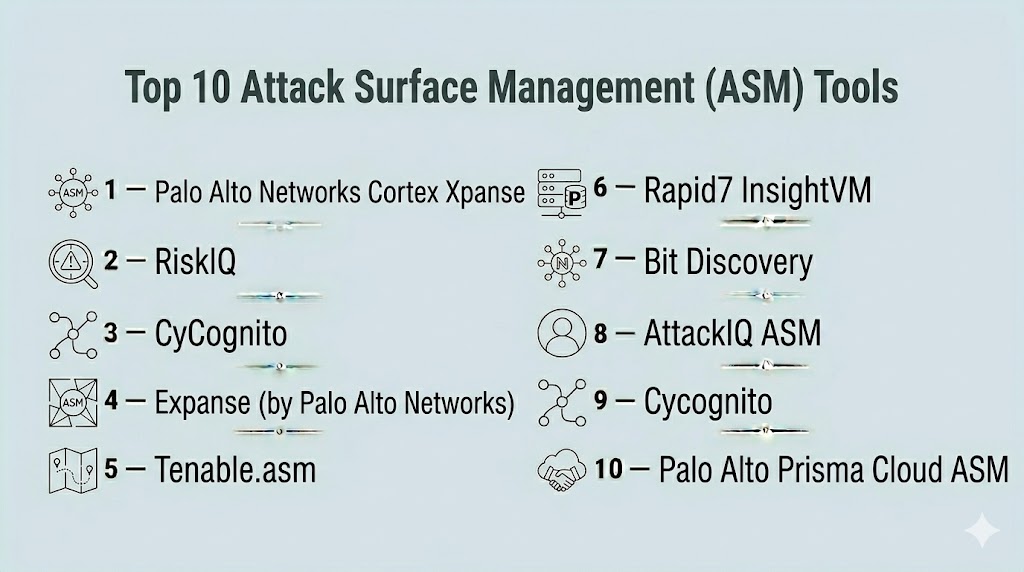
Top 10 Attack Surface Management (ASM) Tools
#1 — Palo Alto Networks Cortex Xpanse
Short description : Cortex Xpanse provides continuous discovery and monitoring of enterprise attack surfaces. It’s designed for security teams seeking real-time visibility into exposed assets across networks, cloud, and SaaS applications.
Key Features
- Continuous internet-wide asset discovery
- External exposure mapping
- Risk-based prioritization
- Integration with SIEM and SOAR platforms
- API access for automation
- Reporting and analytics dashboards
Pros
- Real-time attack surface visibility
- Enterprise-grade scalability
- Strong integration ecosystem
Cons
- Premium pricing
- Complexity for small teams
Platforms / Deployment
- Web-based
- Cloud
Security & Compliance
- SSO, encryption
- Not publicly stated
Integrations & Ecosystem
Integrates with SIEM, SOAR, and vulnerability management platforms.
- Splunk, ServiceNow, Jira
- API for custom workflows
- Cloud and on-premises connectors
Support & Community
- Vendor support tiers
- Documentation and onboarding guides
#2 — RiskIQ
Short description : RiskIQ offers comprehensive external threat detection and attack surface management for enterprises, identifying vulnerabilities, exposed assets, and malicious activity across the digital footprint.
Key Features
- Internet-wide asset discovery
- Threat intelligence correlation
- Cloud and SaaS monitoring
- Risk prioritization dashboards
- API-driven automation
Pros
- Strong threat intelligence integration
- Scales for global enterprises
- Detailed reporting
Cons
- High licensing costs
- Steeper learning curve
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Encryption, RBAC
- Not publicly stated
Integrations & Ecosystem
- Splunk, Jira, ServiceNow
- API for automated workflows
- CI/CD and DevSecOps integrations
Support & Community
- Vendor support
- Extensive documentation
#3 — CyCognito
Short description : CyCognito helps organizations identify unknown or shadow assets, providing actionable insights into security risks and exposures across IT environments.
Key Features
- Continuous external asset discovery
- Shadow IT and unmanaged asset detection
- Risk scoring and prioritization
- Cloud, SaaS, and on-prem monitoring
- Automated alerts
Pros
- Fast identification of unknown assets
- Risk-based prioritization
- Strong cloud and SaaS coverage
Cons
- May require integration for full automation
- Licensing costs for large environments
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM and vulnerability management tools
- APIs for automation
- Cloud platform connectors
Support & Community
- Vendor support
- Knowledge base and documentation
#4 — Expanse (by Palo Alto Networks)
Short description : Expanse provides comprehensive attack surface mapping and exposure visibility, helping security teams discover and monitor assets in real-time across the enterprise.
Key Features
- Internet-exposed asset discovery
- Continuous monitoring
- Integration with SIEM and vulnerability management
- Risk scoring and prioritization
- Automated alerting
Pros
- Enterprise-grade visibility
- Detailed reporting
- Scalable across large organizations
Cons
- Complexity may require training
- Premium pricing
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- SSO, encryption
- Not publicly stated
Integrations & Ecosystem
- Splunk, ServiceNow, Jira
- API access for automated processes
- Vulnerability scanning tools
Support & Community
- Vendor support
- Documentation and training
#5 — Tenable.asm
Short description : Tenable.asm provides attack surface monitoring and discovery to identify and mitigate external exposure, enabling organizations to proactively manage security risks.
Key Features
- External attack surface discovery
- Cloud and on-prem monitoring
- Risk scoring for vulnerabilities
- Integration with SIEM and ticketing systems
- Reporting dashboards
Pros
- Easy risk prioritization
- Scales for mid-size and enterprise organizations
- Good integration options
Cons
- Advanced analytics require additional modules
- Cost may be high for SMBs
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM tools, Jira, ServiceNow
- API integration for automation
- Vulnerability scanning tools
Support & Community
- Vendor support
- Documentation
#6 — Rapid7 InsightVM
Short description : InsightVM by Rapid7 provides attack surface analysis and vulnerability management, helping teams identify exposures and prioritize remediation based on risk.
Key Features
- Asset discovery and monitoring
- Risk scoring and analytics
- Integration with SIEM, SOAR, and ticketing systems
- Cloud and on-prem support
- Automated alerts
Pros
- Combines ASM and vulnerability management
- Strong dashboards and reporting
- Cloud-native deployment
Cons
- Requires configuration for complex environments
- Licensing costs
Platforms / Deployment
- Web
- Cloud / On-prem
Security & Compliance
- Encryption, RBAC
- Not publicly stated
Integrations & Ecosystem
- SIEM tools, Jira, ServiceNow
- API access for automation
- Cloud platform connectors
Support & Community
- Vendor support
- Documentation
#7 — Bit Discovery
Short description : Bit Discovery identifies and manages shadow IT, exposing unknown assets, endpoints, and cloud services across the organization’s attack surface.
Key Features
- Shadow IT discovery
- Asset inventory and monitoring
- Risk-based prioritization
- Continuous exposure alerts
- Cloud service scanning
Pros
- Effective for uncovering unmanaged assets
- Simple dashboards
- Automation-friendly
Cons
- Limited advanced analytics
- Enterprise pricing
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM and vulnerability tools
- APIs for automation
- Ticketing and alerting systems
Support & Community
- Vendor support
- Documentation
#8 — AttackIQ ASM
Short description : AttackIQ ASM provides real-time visibility into attack surfaces, identifying exposures and helping teams reduce risk across IT, cloud, and SaaS environments.
Key Features
- Continuous asset discovery
- Exposure and vulnerability mapping
- Risk scoring dashboards
- Integration with security operations tools
- Automated alerting
Pros
- Real-time monitoring
- Strong reporting and dashboards
- Cloud and SaaS coverage
Cons
- Premium pricing
- May require integration for full automation
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM, SOAR, Jira
- APIs for automation
Support & Community
- Vendor support
- Documentation
#9 — Cycognito
Short description : Cycognito discovers unknown and unmanaged assets, helping security teams understand and mitigate external attack surfaces.
Key Features
- Continuous external asset discovery
- Risk scoring and prioritization
- Shadow IT identification
- Cloud and SaaS monitoring
- Integration with SIEM and ticketing
Pros
- Excellent for discovering unmanaged assets
- Prioritizes remediation based on risk
- Supports cloud and on-prem environments
Cons
- Premium pricing
- Requires setup for complex enterprises
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- SIEM, Jira, ServiceNow
- API access
Support & Community
- Vendor support
- Documentation
#10 — Palo Alto Prisma Cloud ASM
Short description : Prisma Cloud ASM helps organizations continuously monitor and manage cloud and web-facing assets, providing visibility into exposures and risk across hybrid environments.
Key Features
- Cloud asset discovery
- Continuous attack surface monitoring
- Risk scoring and exposure mapping
- Integration with CI/CD and security tools
- Automated alerts
Pros
- Cloud-native and scalable
- Real-time monitoring
- Strong visibility dashboards
Cons
- Complexity in large environments
- Premium pricing
Platforms / Deployment
- Web
- Cloud
Security & Compliance
- Encryption, RBAC
- Not publicly stated
Integrations & Ecosystem
- CI/CD pipelines, SIEM, SOAR
- APIs for automation
Support & Community
- Vendor support
- Documentation
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Cortex Xpanse | Enterprise security teams | Web | Cloud | Real-time external asset discovery | N/A |
| RiskIQ | Large enterprises | Web | Cloud | Threat intelligence-driven ASM | N/A |
| CyCognito | Cloud/SaaS-heavy orgs | Web | Cloud | Shadow IT discovery | N/A |
| Expanse | Enterprise DevOps | Web | Cloud | Comprehensive attack surface mapping | N/A |
| Tenable.asm | Mid-size & enterprise | Web | Cloud | Risk scoring & exposure mapping | N/A |
| InsightVM | Vulnerability & security teams | Web | Cloud / On-prem | ASM + vulnerability management | N/A |
| Bit Discovery | SMB & mid-market | Web | Cloud | Shadow IT & unmanaged asset detection | N/A |
| AttackIQ ASM | Security operations | Web | Cloud | Real-time exposure dashboards | N/A |
| Cycognito | Enterprises with complex IT | Web | Cloud | External asset risk prioritization | N/A |
| Prisma Cloud ASM | Cloud-focused enterprises | Web | Cloud | Continuous cloud asset monitoring | N/A |
Evaluation & Scoring of Attack Surface Management (ASM)
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Cortex Xpanse | 9 | 8 | 9 | 8 | 9 | 8 | 7 | 8.4 |
| RiskIQ | 9 | 7 | 8 | 8 | 8 | 7 | 7 | 8.0 |
| CyCognito | 8 | 8 | 8 | 8 | 8 | 7 | 7 | 7.8 |
| Expanse | 9 | 7 | 8 | 8 | 8 | 7 | 7 | 8.0 |
| Tenable.asm | 8 | 8 | 7 | 8 | 7 | 7 | 7 | 7.6 |
| InsightVM | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Bit Discovery | 7 | 8 | 7 | 7 | 7 | 7 | 7 | 7.2 |
| AttackIQ ASM | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Cycognito | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Prisma Cloud ASM | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
Interpretation: Weighted scores provide a comparative overview of ASM tools across core functionality, ease of use, integrations, security, performance, support, and value. Higher scores indicate broader suitability, but selection should consider specific organizational needs, cloud environments, and regulatory requirements.
Which Attack Surface Management (ASM) Tool Is Right for You?
Solo / Freelancer
Lightweight or SaaS-first tools like Bit Discovery or Cycognito provide fast visibility and risk insights without complex setup.
SMB
Tenable.asm, AttackIQ ASM, or Prisma Cloud ASM balance affordability with sufficient coverage for cloud and web-facing assets.
Mid-Market
InsightVM, CyCognito, or RiskIQ provide advanced discovery, risk scoring, and integration with CI/CD and security tools.
Enterprise
Cortex Xpanse, Expanse, and RiskIQ scale across large IT environments, providing continuous monitoring, comprehensive dashboards, and integration with SIEM and SOAR.
Budget vs Premium
Open SaaS or SMB-friendly tools deliver essential ASM capabilities; premium enterprise tools justify higher costs through scalability, analytics, and compliance reporting.
Feature Depth vs Ease of Use
Small teams prioritize ease of deployment and usability; enterprises benefit from rich features, risk analytics, and automation support.
Integrations & Scalability
Large organizations should focus on tools like Cortex Xpanse and RiskIQ that integrate with SIEM, vulnerability management, and cloud platforms.
Security & Compliance Needs
Regulated industries require encryption, RBAC, audit logging, and compliance reporting for GDPR, HIPAA, and ISO 27001.
Frequently Asked Questions (FAQs)
1. What pricing models exist for ASM tools?
Most offer subscription-based SaaS or enterprise licensing. SMB-focused solutions may have lower-cost plans.
2. How long does onboarding take?
Small teams can onboard in days; large enterprise deployments may require weeks for configuration and integration.
3. Can ASM tools integrate with CI/CD pipelines?
Yes, most tools integrate with Jenkins, GitHub Actions, GitLab, and Azure DevOps.
4. Do ASM tools cover cloud and SaaS assets?
Yes, leading tools scan cloud infrastructure, SaaS applications, and web-facing services.
5. How often do tools update asset discovery?
Top ASM tools provide continuous or near real-time monitoring for dynamic environments.
6. Are ASM tools suitable for regulated industries?
Yes, tools often support compliance reporting, encryption, and audit trails for HIPAA, GDPR, and ISO standards.
7. Can ASM tools prioritize risks?
Yes, risk-based scoring helps teams focus on the most exploitable or critical exposures.
8. Do they identify shadow IT or unmanaged assets?
Enterprise-focused tools like CyCognito and Bit Discovery excel at discovering unknown assets.
9. Can small teams benefit from ASM tools?
Yes, lightweight SaaS tools provide actionable insights without heavy enterprise overhead.
10. How do I choose the best ASM tool?
Consider team size, cloud adoption, regulatory requirements, integration needs, and budget when shortlisting.
Conclusion
Attack Surface Management tools are critical for modern security programs, providing visibility, risk prioritization, and proactive defense across complex digital environments. SMBs and developers can benefit from tools like Bit Discovery and Cycognito, while large enterprises gain maximum value from Cortex Xpanse, RiskIQ, and Expanse, which offer scalability, automation, and advanced analytics. Selection should align with organizational size, cloud adoption, regulatory requirements, and integration needs. Teams should pilot solutions, validate their asset discovery and risk scoring, and ensure integration with existing security workflows to strengthen overall cybersecurity posture.
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals