Introduction
Deception technology tools are cybersecurity solutions that create decoys, traps, and lures to detect, misdirect, and analyze malicious activity within an organization’s IT environment. By simulating real assets, endpoints, or applications, these tools help identify attackers early, gather intelligence on tactics, and prevent lateral movement.
In , the rise of advanced persistent threats (APTs), ransomware, and insider threats has made deception technologies critical for proactive defense. They provide early warning signals, reduce dwell time of attackers, and integrate into broader security operations for actionable insights.
Real-world use cases:
- Detecting unauthorized access attempts across endpoints and networks
- Luring attackers into honeypots to study their methods
- Identifying insider threats by monitoring access to decoy assets
- Preventing lateral movement in compromised networks
- Enhancing SIEM and threat intelligence feeds
Evaluation criteria:
- Variety and realism of decoy assets
- Automation and orchestration capabilities
- Integration with SIEM, SOAR, and endpoint security
- Threat detection accuracy and false-positive management
- Analytics, reporting, and intelligence outputs
- Scalability and coverage across cloud, on-prem, and hybrid networks
- Deployment flexibility (cloud, on-prem, hybrid)
- Ease of management and visibility dashboards
- Compliance and audit readiness
- Licensing, cost, and total cost of ownership
Best for: Security operations teams, large enterprises, and organizations facing sophisticated cyber threats.
Not ideal for: Small businesses with limited IT security budgets or minimal network exposure; alternative security tools may suffice.
Key Trends in Deception Technology Tools
- AI-driven decoy generation and threat pattern analysis
- Integration with SOAR and SIEM platforms for automated incident response
- Multi-layered deception including endpoints, servers, applications, and cloud services
- Use of behavioral analytics to differentiate real activity from decoy interaction
- Automated alerting and threat intelligence sharing across SOCs
- Hybrid and cloud-native deployment for flexible scaling
- Subscription and consumption-based pricing models
- Convergence with EDR/XDR for comprehensive detection
- Focus on detecting insider threats and lateral movement
- Enhanced reporting and compliance features for regulatory standards
How We Selected These Tools (Methodology)
- Market adoption and vendor mindshare
- Feature richness, including decoy types, orchestration, and analytics
- Reliability and real-world performance metrics
- Security posture, including encryption, access controls, and audit logs
- Integration capabilities with SIEM, SOAR, endpoint, and cloud security
- Scalability and suitability for SMB, mid-market, and enterprise
- Deployment flexibility (cloud, on-prem, hybrid)
- Automation and alerting capabilities
- Threat intelligence and reporting functionalities
- Total cost of ownership and support ecosystem
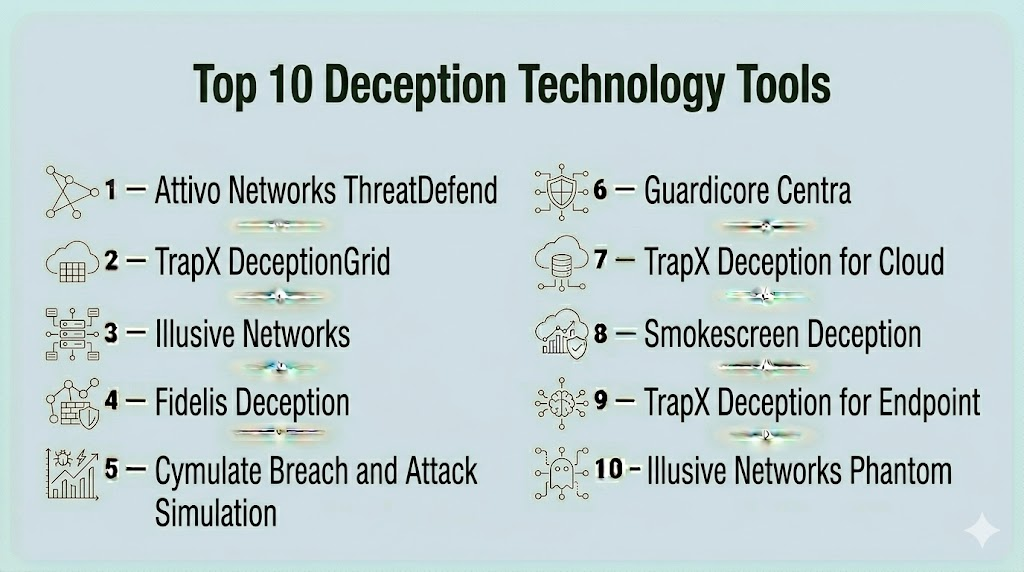
Top 10 Deception Technology Tools
#1 — Attivo Networks ThreatDefend
Short description : ThreatDefend creates realistic decoys and traps across endpoints, servers, and network segments, detecting lateral movement and insider threats. Ideal for large enterprises seeking proactive detection.
Key Features
- Endpoint and server decoys
- Active directory protection
- Lateral movement detection
- Automated alerting and remediation
- Centralized dashboard and analytics
Pros
- Early detection of threats
- Integrates with SIEM/XDR platforms
- Reduces dwell time for attackers
Cons
- Premium pricing
- Complexity in initial deployment
Platforms / Deployment
- Windows, Linux
- Cloud / On-prem / Hybrid
Security & Compliance
- SSO/SAML, MFA, encryption, RBAC
- SOC 2, ISO 27001
Integrations & Ecosystem
- SIEM, SOAR, EDR integrations
- API automation
- Threat intelligence feeds
Support & Community
- Vendor support, training, documentation
#2 — TrapX DeceptionGrid
Short description : Offers network-wide deception using honeypots, traps, and lures, with deep attack analysis for SOC teams.
Key Features
- Network and endpoint decoys
- Automated attack path visualization
- Threat analytics and reporting
- Real-time alerting
- Active attack simulation
Pros
- High-fidelity decoys
- Strong analytics and SOC integration
- Flexible deployment
Cons
- Learning curve for small teams
- Licensing costs
Platforms / Deployment
- Windows, Linux
- Cloud / On-prem
Security & Compliance
- Encryption, RBAC, audit logs
- Not publicly stated
Integrations & Ecosystem
- SIEM, SOAR
- API access for automation
- Security orchestration
Support & Community
- Vendor support, training materials
#3 — Illusive Networks
Short description : Focuses on identity-centric deception, targeting credential theft and lateral movement, with decoys in endpoints and network segments.
Key Features
- Identity deception
- Credential and session traps
- Lateral movement detection
- Automated alerting
- Integration with threat intelligence platforms
Pros
- Focused on insider and APT detection
- Automated incident insights
- Scalable across enterprise networks
Cons
- Limited endpoint coverage for SMB
- Premium pricing
Platforms / Deployment
- Windows, Linux
- Cloud / On-prem / Hybrid
Security & Compliance
- SSO/SAML, encryption
- SOC 2
Integrations & Ecosystem
- SIEM, SOAR, IAM integrations
- APIs for orchestration
Support & Community
- Vendor support, documentation
#4 — Fidelis Deception
Short description : Provides decoy systems for endpoints, servers, and cloud resources, detecting advanced threats and zero-day attacks.
Key Features
- Multi-environment decoy deployment
- Automated threat alerting
- Analytics for attack path and tactics
- Active response and mitigation
- Integration with Fidelis XDR
Pros
- Detects sophisticated attacks
- Centralized monitoring
- Real-time alerts
Cons
- Complexity in configuration
- Additional modules needed for full coverage
Platforms / Deployment
- Windows, Linux
- Cloud / On-prem
Security & Compliance
- Encryption, RBAC
- SOC 2
Integrations & Ecosystem
- SIEM, XDR, SOAR
- API extensibility
Support & Community
- Vendor support, training
#5 — Cymulate Breach and Attack Simulation
Short description : Uses automated simulations and deception scenarios to test defenses and validate detection capabilities.
Key Features
- Automated attack simulations
- Endpoint and network decoys
- Breach validation
- Threat analytics
- Reporting and dashboards
Pros
- Continuous validation of defenses
- Integrates with SOC workflows
- Cloud-native
Cons
- Less focus on production deception
- Premium subscription
Platforms / Deployment
- Windows, Linux
- Cloud
Security & Compliance
- Encryption, MFA
- Not publicly stated
Integrations & Ecosystem
- SIEM, SOAR
- Threat intelligence feeds
Support & Community
- Vendor support, documentation
#6 — Guardicore Centra
Short description : Provides micro-segmentation and deception to detect lateral movement in hybrid and cloud environments.
Key Features
- Network micro-segmentation
- Endpoint decoys
- Lateral movement detection
- Threat analytics
- Automated response
Pros
- Reduces attack surface
- Early detection of advanced threats
- Integrates with existing security stack
Cons
- Initial deployment complexity
- Licensing cost
Platforms / Deployment
- Windows, Linux
- Cloud / On-prem / Hybrid
Security & Compliance
- Encryption, RBAC
- ISO 27001
Integrations & Ecosystem
- SIEM, SOAR, IAM
- API access
Support & Community
- Vendor support, documentation
#7 — TrapX Deception for Cloud
Short description : Cloud-focused deception platform protecting SaaS, IaaS, and hybrid environments from lateral movement and insider threats.
Key Features
- Cloud-native decoys
- SaaS application traps
- Threat analytics
- Real-time alerts
- Integration with SOC tools
Pros
- Protects cloud and hybrid environments
- Early threat detection
- Scalable globally
Cons
- Requires cloud expertise
- Premium subscription
Platforms / Deployment
- Cloud
- Cloud-native
Security & Compliance
- Encryption, RBAC
- Not publicly stated
Integrations & Ecosystem
- SIEM, SOAR, IAM
- API integrations
Support & Community
- Vendor support
#8 — Smokescreen Deception
Short description : Enterprise-grade platform deploying decoy endpoints and networks, analyzing attacker behavior.
Key Features
- Endpoint decoys
- Network traps
- Attack analytics
- Threat scoring
- Automated alerts
Pros
- Effective for advanced threats
- Detailed attack intelligence
- Integrates with SOC
Cons
- Deployment overhead
- Pricing for large environments
Platforms / Deployment
- Windows, Linux
- On-prem / Hybrid
Security & Compliance
- Encryption, RBAC
- Not publicly stated
Integrations & Ecosystem
- SIEM, SOAR
- APIs for automation
Support & Community
- Vendor support, documentation
#9 — TrapX Deception for Endpoint
Short description : Focused on endpoint-level decoys and honeytokens to detect attacks before they spread.
Key Features
- Endpoint decoys
- File and credential traps
- Threat analytics
- Automated alerting
- Centralized dashboard
Pros
- Early endpoint attack detection
- Integrates with EDR/SIEM
- Scalable for large networks
Cons
- Limited network deception
- Subscription costs
Platforms / Deployment
- Windows, macOS
- Cloud / On-prem
Security & Compliance
- Encryption, MFA
- Not publicly stated
Integrations & Ecosystem
- EDR, SIEM, SOAR
- API extensibility
Support & Community
- Vendor support
#10 — Illusive Networks Phantom
Short description : Provides high-fidelity endpoint and network deception, detecting credential theft and lateral movement in enterprise environments.
Key Features
- Identity and credential deception
- Endpoint and network decoys
- Automated alerting and remediation
- Analytics for attacker behavior
- Integration with SOC platforms
Pros
- Strong insider threat detection
- Centralized monitoring
- Automated responses
Cons
- Premium licensing
- Deployment complexity
Platforms / Deployment
- Windows, Linux
- Cloud / On-prem
Security & Compliance
- SSO/SAML, encryption
- SOC 2
Integrations & Ecosystem
- SIEM, SOAR, IAM
- API automation
Support & Community
- Vendor support, documentation
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Attivo Networks ThreatDefend | Enterprise | Windows, Linux | Cloud / On-prem / Hybrid | Identity & endpoint decoys | N/A |
| TrapX DeceptionGrid | Enterprise | Windows, Linux | Cloud / On-prem | Network honeypots | N/A |
| Illusive Networks | Enterprise | Windows, Linux | Cloud / On-prem / Hybrid | Identity-centric deception | N/A |
| Fidelis Deception | Enterprise | Windows, Linux | Cloud / On-prem | Multi-environment decoys | N/A |
| Cymulate BAS | Enterprise | Windows, Linux | Cloud | Breach simulations + decoys | N/A |
| Guardicore Centra | Enterprise | Windows, Linux | Cloud / On-prem / Hybrid | Micro-segmentation & deception | N/A |
| TrapX Deception Cloud | Enterprise | Cloud | Cloud-native | Cloud SaaS decoys | N/A |
| Smokescreen Deception | Enterprise | Windows, Linux | On-prem / Hybrid | Network & endpoint deception | N/A |
| TrapX Endpoint | Enterprise | Windows, macOS | Cloud / On-prem | Endpoint decoys & honeytokens | N/A |
| Illusive Phantom | Enterprise | Windows, Linux | Cloud / On-prem | Credential & identity deception | N/A |
Evaluation & Scoring of Deception Technology Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Attivo Networks ThreatDefend | 9 | 8 | 9 | 9 | 9 | 8 | 7 | 8.4 |
| TrapX DeceptionGrid | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Illusive Networks | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Fidelis Deception | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Cymulate BAS | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Guardicore Centra | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| TrapX Deception Cloud | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Smokescreen Deception | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| TrapX Endpoint | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Illusive Phantom | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
Scores are comparative across features, usability, integrations, security, performance, support, and value.
Which Deception Technology Tool Is Right for You?
Solo / Freelancer
Lightweight cloud-native options like Cymulate BAS offer simple deployment and automated attack simulations.
SMB
TrapX DeceptionGrid and Fidelis Deception provide network and endpoint decoys suitable for medium-sized enterprises.
Mid-Market
Attivo Networks ThreatDefend, Guardicore Centra, and Illusive Networks deliver scalable deception for hybrid infrastructures.
Enterprise
Illusive Phantom, TrapX Deception Cloud, and Smokescreen Deception provide full-scale multi-layered deception with advanced analytics.
Budget vs Premium
SMBs may opt for entry-level cloud simulations; enterprises require comprehensive deception across endpoints, networks, and cloud.
Feature Depth vs Ease of Use
Smaller teams benefit from automated setups; larger teams gain value from detailed decoy orchestration, analytics, and integration.
Integrations & Scalability
Enterprise-grade tools integrate with SIEM, SOAR, EDR, IAM, and cloud services for wide coverage.
Security & Compliance Needs
Critical for organizations in regulated industries requiring audit trails, SOC 2, ISO 27001, GDPR compliance, and early threat detection.
Frequently Asked Questions (FAQs)
1. What is deception technology?
Deception technology creates decoys, honeypots, and traps to detect malicious activity and provide early warnings.
2. Can small businesses use these tools?
Yes, lightweight cloud-based deception tools provide affordable detection for smaller networks.
3. How is deception different from traditional security?
Traditional security blocks threats; deception proactively detects attackers within the environment by engaging them with decoys.
4. Do these tools integrate with SIEM?
Yes, most integrate with SIEM and SOAR platforms for automated alerts and incident response.
5. Can they detect insider threats?
Absolutely, decoy endpoints and honeytokens help identify lateral movement and unauthorized access.
6. Are they suitable for cloud environments?
Yes, cloud-native deception platforms protect SaaS, IaaS, and hybrid environments.
7. What is the cost model?
Varies by vendor; typically subscription-based with enterprise licensing options.
8. How difficult is deployment?
Cloud-native solutions are faster to deploy; on-prem or hybrid environments may require planning.
9. Do they provide analytics?
Yes, most provide dashboards, attack path analysis, and reporting for security operations.
10. Can deception tools replace antivirus or firewalls?
No, they complement existing security solutions by detecting threats that bypass preventive controls.
Conclusion
Deception technology tools are essential for proactive threat detection and early warning in modern enterprise environments. From small SMBs leveraging cloud-based simulations to global enterprises deploying multi-layered decoy networks, these platforms reduce dwell time, identify advanced threats, and enhance SOC capabilities. Organizations should evaluate their network complexity, threat landscape, and integration needs, pilot a shortlist of solutions, and implement a layered approach to detect and mitigate sophisticated cyber attacks effectively.
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals