Introduction
Digital forensics tools are specialized cybersecurity solutions designed to investigate, analyze, and recover data from digital devices and networks after a security incident. These tools help organizations reconstruct events, identify perpetrators, and preserve evidence for legal, compliance, or internal review purposes.
In , with the proliferation of cyberattacks, insider threats, and sophisticated ransomware campaigns, digital forensics has become crucial for both reactive and proactive security strategies. These tools not only assist in incident response and breach investigation, but also in compliance with regulations like GDPR, HIPAA, and SOC 2.
Real-world use cases:
- Investigating ransomware or malware attacks
- Conducting insider threat investigations
- Performing endpoint and network forensic analysis
- Preserving and analyzing cloud-based or SaaS data
- Supporting legal proceedings with chain-of-custody evidence
Evaluation criteria:
- Device and OS coverage
- Cloud, SaaS, and endpoint data support
- Real-time and historical analysis capabilities
- Integration with SIEM, SOAR, and EDR
- Evidence preservation and reporting quality
- Automation and workflow orchestration
- Compliance and audit readiness
- Scalability and performance
- Deployment options and ease of use
- Licensing and total cost of ownership
Best for: SOC teams, incident response units, legal/compliance teams, and enterprises with high data sensitivity.
Not ideal for: Small organizations with minimal digital footprint or low security risk; simpler backup and monitoring tools may suffice.
Key Trends in Digital Forensics Tools
- AI-assisted forensic analysis for faster threat attribution
- Cloud-native forensics supporting SaaS and IaaS environments
- Automation in evidence collection and reporting
- Integration with SIEM, SOAR, and XDR for comprehensive incident response
- Real-time monitoring and alerts for endpoint and network anomalies
- Cross-platform support including mobile and IoT devices
- Compliance-focused features for GDPR, HIPAA, and SOC frameworks
- Subscription and SaaS pricing models for easier adoption
- Convergence with threat intelligence for proactive detection
- Enhanced reporting dashboards with chain-of-custody tracking
How We Selected These Tools (Methodology)
- Market adoption and vendor reputation
- Feature depth and completeness for multiple device types
- Reliability and accuracy of data collection and analysis
- Security posture including encryption, RBAC, and audit trails
- Integration with SOC, SIEM, SOAR, and forensic ecosystems
- Suitability across SMB, mid-market, and enterprise segments
- Automation capabilities for investigation workflows
- Deployment flexibility (cloud, on-prem, hybrid)
- Scalability for high-volume incident investigations
- Vendor support, training, and documentation quality
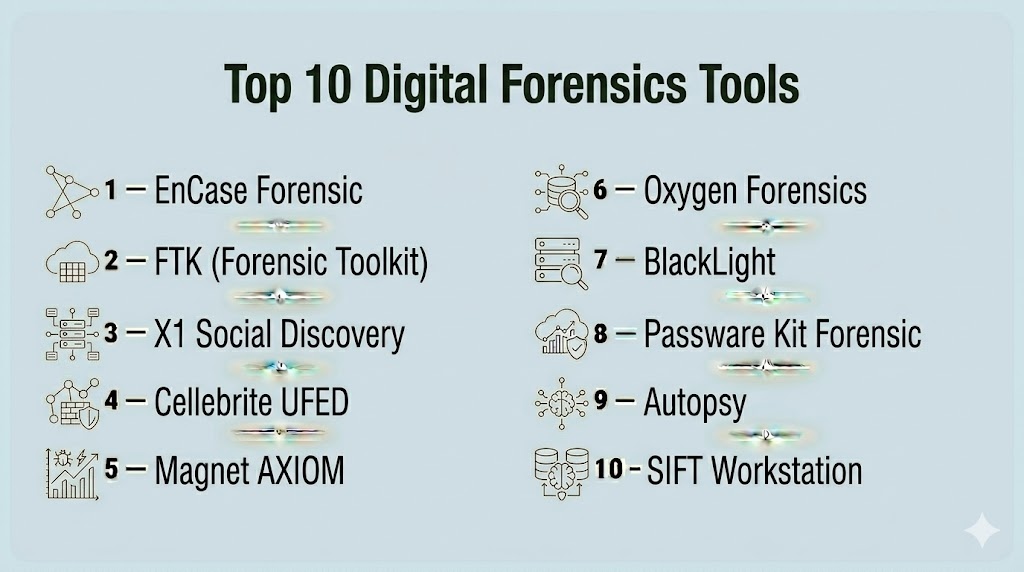
Top 10 Digital Forensics Tools
#1 — EnCase Forensic
Short description : EnCase Forensic provides comprehensive endpoint and disk analysis, allowing investigators to recover, preserve, and analyze data efficiently. Ideal for enterprises and law enforcement.
Key Features
- Deep disk-level data acquisition
- File signature and metadata analysis
- Automated evidence preservation
- Reporting and chain-of-custody support
- Integration with case management systems
Pros
- Reliable and widely trusted in forensics
- Supports complex investigations
- Strong legal compliance features
Cons
- Steeper learning curve
- Higher licensing cost
Platforms / Deployment
- Windows
- On-prem / Hybrid
Security & Compliance
- Encryption, RBAC, audit logs
- SOC 2, ISO 27001
Integrations & Ecosystem
- Case management systems
- SIEM and EDR tools
- API access for automation
Support & Community
- Vendor training, documentation, professional community
#2 — FTK (Forensic Toolkit)
Short description : FTK allows rapid indexing and deep file analysis across multiple endpoints, supporting legal investigations and cybersecurity incident response.
Key Features
- Comprehensive file and email analysis
- Hash analysis and indexing
- Data carving and recovery
- Real-time monitoring
- Integration with SIEM and incident response platforms
Pros
- Fast data processing
- Comprehensive analysis tools
- Legal evidence readiness
Cons
- Requires significant hardware resources
- Complex setup
Platforms / Deployment
- Windows
- On-prem / Hybrid
Security & Compliance
- Encryption, RBAC
- Not publicly stated
Integrations & Ecosystem
- SIEM, case management, XDR
- Automation APIs
Support & Community
- Documentation and vendor support
#3 — X1 Social Discovery
Short description : X1 Social Discovery is focused on social media and cloud content investigation, enabling fast search and collection for legal and compliance purposes.
Key Features
- Social media data capture
- Email and cloud data collection
- Advanced search capabilities
- Reporting and chain-of-custody documentation
- Cloud and SaaS integration
Pros
- Specialized for social and cloud investigations
- Quick data retrieval
- Legal-ready reporting
Cons
- Limited endpoint support
- Subscription costs
Platforms / Deployment
- Windows
- Cloud / Hybrid
Security & Compliance
- Encryption, audit logs
- Not publicly stated
Integrations & Ecosystem
- Cloud platforms and email providers
- Case management integrations
Support & Community
- Vendor documentation, onboarding support
#4 — Cellebrite UFED
Short description : Cellebrite UFED is designed for mobile device forensics, including smartphones, tablets, and IoT devices, widely used in law enforcement and corporate investigations.
Key Features
- Mobile device data extraction
- Application and message parsing
- Cloud backup retrieval
- Secure evidence preservation
- Reporting and analysis tools
Pros
- Strong mobile forensic capabilities
- Supports iOS and Android
- Secure evidence handling
Cons
- High licensing and maintenance cost
- Requires specialized training
Platforms / Deployment
- Windows
- On-prem / Hybrid
Security & Compliance
- Encryption, audit trails
- SOC 2, ISO 27001
Integrations & Ecosystem
- Mobile management platforms
- SIEM and case management integration
Support & Community
- Vendor support, professional training
#5 — Magnet AXIOM
Short description : Magnet AXIOM provides comprehensive digital investigations across endpoints, mobile devices, and cloud, combining analysis, reporting, and evidence preservation.
Key Features
- Multi-device acquisition
- Cloud account analysis
- Timeline and artifact correlation
- Case management integration
- Reporting for legal compliance
Pros
- Multi-platform support
- Advanced timeline analysis
- Integration-ready
Cons
- Requires high system resources
- Subscription costs
Platforms / Deployment
- Windows
- On-prem / Hybrid
Security & Compliance
- Encryption, RBAC
- SOC 2
Integrations & Ecosystem
- Cloud services, SIEM
- Case management systems
Support & Community
- Vendor support, documentation
#6 — Oxygen Forensics
Short description : Focused on mobile and cloud forensics, Oxygen Forensics enables comprehensive investigations for enterprise and law enforcement.
Key Features
- Mobile device data extraction
- Cloud storage analysis
- App data parsing
- Reporting and chain-of-custody
- Analytics for artifacts
Pros
- Strong mobile support
- Cloud data integration
- Detailed analytics
Cons
- Complex setup for large investigations
- Licensing costs
Platforms / Deployment
- Windows
- On-prem / Hybrid
Security & Compliance
- Encryption, audit logs
- Not publicly stated
Integrations & Ecosystem
- Cloud platforms
- SIEM, case management APIs
Support & Community
- Vendor support, onboarding materials
#7 — BlackLight
Short description : BlackLight specializes in computer and mobile forensics, providing advanced analysis and reporting for legal investigations.
Key Features
- File system and memory analysis
- Mobile and desktop investigation
- Artifact correlation and timeline analysis
- Reporting and evidence management
- Integration with case tools
Pros
- Strong desktop and mobile forensic capabilities
- Comprehensive reporting
- Legal-ready evidence handling
Cons
- Limited cloud-native capabilities
- Learning curve
Platforms / Deployment
- Windows, macOS
- On-prem
Security & Compliance
- Encryption, RBAC
- SOC 2
Integrations & Ecosystem
- Case management, SIEM
- API extensibility
Support & Community
- Vendor documentation, training
#8 — Passware Kit Forensic
Short description : Focuses on password recovery and encrypted data access, complementing other forensic investigations.
Key Features
- Password recovery for files and devices
- Encryption handling
- Evidence preservation
- Reporting and case export
- Supports multiple file types
Pros
- Speeds access to encrypted data
- Integrates with other forensic tools
- Supports multiple platforms
Cons
- Specialized tool, not standalone solution
- Limited device coverage
Platforms / Deployment
- Windows, macOS
- On-prem
Security & Compliance
- Encryption
- Not publicly stated
Integrations & Ecosystem
- Other forensic suites
- Case management APIs
Support & Community
- Vendor support, documentation
#9 — Autopsy
Short description : Open-source digital forensics platform focused on disk and file system analysis, widely used for research, law enforcement, and SMB investigations.
Key Features
- Disk image analysis
- Timeline and keyword search
- File and metadata parsing
- Reporting and artifact correlation
- Extensible via modules
Pros
- Free and open-source
- Flexible for custom workflows
- Active developer community
Cons
- Requires technical expertise
- Limited automation
Platforms / Deployment
- Windows, Linux, macOS
- On-prem
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Modular extensions
- APIs for workflow automation
Support & Community
- Community support, documentation
#10 — SIFT Workstation
Short description : Open-source forensic workstation for advanced incident response and disk analysis, maintained by the SANS Institute.
Key Features
- Disk and file system analysis
- Timeline reconstruction
- Memory analysis
- Artifact correlation
- Supports forensic scripts
Pros
- Free and highly extensible
- Advanced analysis tools
- Trusted in incident response community
Cons
- Requires expertise to configure
- Limited GUI for beginners
Platforms / Deployment
- Linux
- On-prem
Security & Compliance
- Not publicly stated
Integrations & Ecosystem
- Forensic scripts, community modules
Support & Community
- Community support, SANS resources
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| EnCase Forensic | Enterprise | Windows | On-prem / Hybrid | Endpoint & disk analysis | N/A |
| FTK | Enterprise | Windows | On-prem / Hybrid | Fast indexing & file analysis | N/A |
| X1 Social Discovery | Legal / Cloud | Windows | Cloud / Hybrid | Social & cloud data | N/A |
| Cellebrite UFED | Mobile Forensics | Windows | On-prem / Hybrid | Mobile device extraction | N/A |
| Magnet AXIOM | Enterprise | Windows | On-prem / Hybrid | Multi-device & cloud analysis | N/A |
| Oxygen Forensics | Mobile & Cloud | Windows | On-prem / Hybrid | Cloud & app data analysis | N/A |
| BlackLight | Enterprise | Windows, macOS | On-prem | Desktop & mobile analysis | N/A |
| Passware Kit Forensic | Encryption & Passwords | Windows, macOS | On-prem | Password recovery & decryption | N/A |
| Autopsy | SMB / Research | Windows, Linux, macOS | On-prem | Open-source disk analysis | N/A |
| SIFT Workstation | Incident Response | Linux | On-prem | Advanced disk & memory analysis | N/A |
Evaluation & Scoring of Digital Forensics Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| EnCase Forensic | 9 | 8 | 8 | 9 | 9 | 8 | 7 | 8.3 |
| FTK | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.5 |
| X1 Social Discovery | 8 | 8 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Cellebrite UFED | 9 | 7 | 7 | 9 | 8 | 8 | 7 | 8.0 |
| Magnet AXIOM | 9 | 8 | 8 | 8 | 8 | 8 | 7 | 8.0 |
| Oxygen Forensics | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.5 |
| BlackLight | 8 | 7 | 7 | 8 | 8 | 7 | 7 | 7.5 |
| Passware Kit Forensic | 7 | 8 | 7 | 7 | 7 | 7 | 7 | 7.2 |
| Autopsy | 7 | 6 | 6 | 7 | 7 | 6 | 8 | 6.9 |
| SIFT Workstation | 8 | 6 | 6 | 7 | 7 | 6 | 8 | 7.0 |
Scores are comparative across core features, usability, integrations, security, performance, support, and value.
Which Digital Forensics Tool Is Right for You?
Solo / Freelancer
Open-source tools like Autopsy and SIFT Workstation offer accessible, lightweight forensic capabilities.
SMB
FTK, X1 Social Discovery, and Passware Kit provide scalable solutions for small to mid-sized organizations.
Mid-Market
Magnet AXIOM, Oxygen Forensics, and BlackLight offer comprehensive forensic capabilities across endpoints, mobile, and cloud.
Enterprise
EnCase Forensic, Cellebrite UFED, and Magnet AXIOM deliver multi-device, multi-environment coverage with advanced analytics.
Budget vs Premium
Smaller teams benefit from open-source or modular solutions; enterprises often require full-featured suites with advanced reporting and legal compliance.
Feature Depth vs Ease of Use
Cloud-native or modular tools allow faster deployment, whereas enterprise suites provide deep investigative and reporting features.
Integrations & Scalability
Enterprise-grade tools integrate with SIEM, SOAR, EDR, and case management for comprehensive investigations.
Security & Compliance Needs
Organizations must ensure proper encryption, RBAC, audit trails, and regulatory compliance for evidence handling.
Frequently Asked Questions (FAQs)
1. What is digital forensics?
Digital forensics investigates and recovers data from devices, networks, and cloud environments after a security incident.
2. Can small businesses use these tools?
Yes, open-source and modular tools like Autopsy and SIFT Workstation provide cost-effective solutions.
3. How do digital forensics tools differ from standard monitoring?
They focus on data recovery, analysis, and legal-grade evidence, rather than just prevention or detection.
4. Do these tools support cloud environments?
Yes, several tools support SaaS, IaaS, and hybrid cloud forensics.
5. Can they handle mobile devices?
Tools like Cellebrite UFED and Oxygen Forensics specialize in mobile device data extraction.
6. Are they suitable for legal proceedings?
Yes, most provide chain-of-custody, reporting, and compliance features suitable for court evidence.
7. What is the typical cost model?
Costs vary: subscription, license-based, or open-source options exist depending on features and scale.
8. Is specialized training required?
Some enterprise tools require training for advanced forensic techniques.
9. Can they detect insider threats?
Yes, by analyzing user activity, endpoints, and cloud access patterns.
10. Do they replace antivirus or EDR solutions?
No, they complement existing security tools by providing investigative and forensic capabilities.
Conclusion
Digital forensics tools are essential for investigating cyber incidents, preserving evidence, and supporting compliance. From SMB-friendly open-source options to enterprise-grade multi-device suites, these platforms enable teams to detect, analyze, and remediate security breaches effectively. Organizations should assess their environment, deploy a pilot, and integrate with existing security infrastructure to ensure accurate, efficient forensic investigations.
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals