Introduction
Zero Trust Network Access (ZTNA) is a modern security framework that assumes no user or device is inherently trustworthy. It provides secure, context-aware access to applications and resources, replacing legacy VPNs with granular, policy-driven controls. In a hybrid and remote work environment, ZTNA ensures that users only access the resources they are explicitly authorized to, minimizing risk and attack surfaces.
In ZTNA adoption has accelerated due to remote workforce expansion, cloud migration, and increasing cyber threats. Organizations are implementing ZTNA to secure sensitive applications, enforce least-privilege access, and maintain compliance across distributed IT environments.
Real-world use cases include:
- Securing access for remote and hybrid employees
- Enforcing least-privilege access to cloud applications and on-premises resources
- Reducing lateral movement of threats inside the network
- Integrating with identity providers for adaptive access control
- Monitoring user behavior and detecting anomalies
Key criteria for evaluation:
- Granular application access control
- Context-aware authentication (device, location, risk)
- Integration with IAM and MFA solutions
- Real-time monitoring and logging
- Ease of deployment and scalability
- Policy automation and orchestration
- Cloud and on-premises resource coverage
- Compliance support (GDPR, HIPAA, SOC 2, ISO 27001)
- Threat detection and anomaly alerts
Best for: Security, IT, and compliance teams in enterprises, SMBs with cloud adoption, and organizations with remote/hybrid workforces.
Not ideal for: Organizations with minimal remote access needs or fully on-premises IT environments.
Key Trends in ZTNA
- AI-driven adaptive authentication and anomaly detection
- Cloud-native ZTNA integrated with multi-cloud environments
- Integration with CASB, SWG, and endpoint security solutions
- Zero Trust policy orchestration across hybrid networks
- API-based automation for access requests and approvals
- User behavior analytics for continuous trust assessment
- Granular least-privilege access enforcement
- Simplified deployment for remote and hybrid teams
- Context-aware access based on device posture, geolocation, and risk
- Subscription and usage-based licensing models
How We Selected These Tools (Methodology)
- Evaluated market adoption and industry mindshare for ZTNA solutions
- Reviewed feature completeness including adaptive access, policy automation, and integration
- Assessed reliability and performance signals in distributed networks
- Verified security posture: encryption, audit logs, RBAC
- Considered integrations with IAM, SWG, endpoint security, and cloud services
- Balanced enterprise, SMB, and hybrid-ready solutions
- Evaluated ease of deployment, configuration, and management
- Checked compliance and reporting capabilities
- Reviewed vendor support and community engagement
- Assessed licensing and total cost of ownership
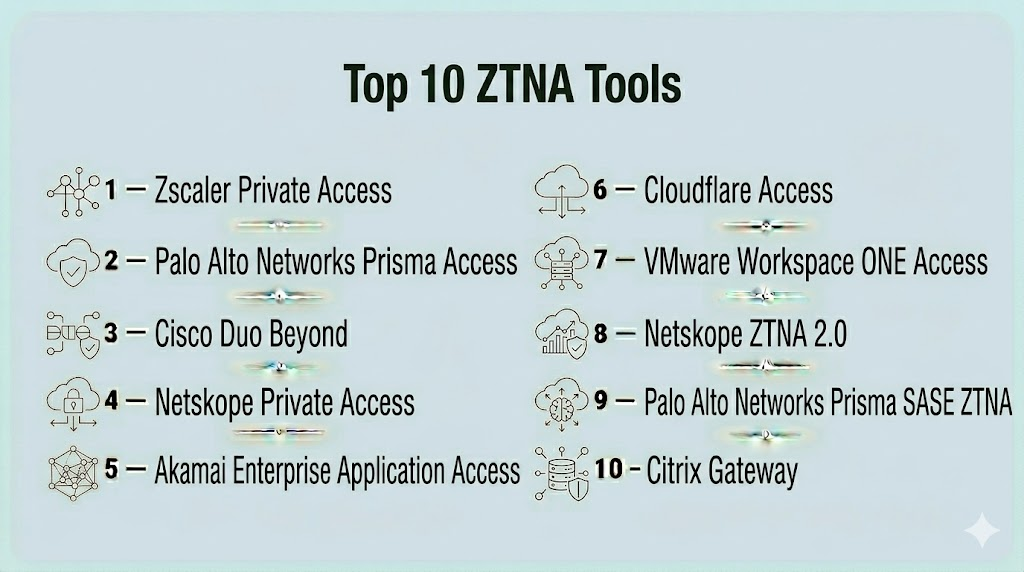
Top 10 ZTNA Tools
#1 — Zscaler Private Access
Short description : Zscaler Private Access (ZPA) provides seamless, secure, and policy-driven access to applications without exposing the network. Ideal for enterprises adopting cloud-first architectures.
Key Features
- Zero Trust access for internal applications
- Identity-based access controls
- Application segmentation
- Real-time policy enforcement
- Cloud-native architecture
Pros
- Scalable cloud deployment
- Reduces attack surface
- Strong integration with identity providers
Cons
- Premium pricing
- Complexity in large deployments
Platforms / Deployment
- Web, Windows, macOS
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, RBAC
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Azure AD, Okta, Ping Identity
- SIEM and endpoint security
- API-based automation
Support & Community
- Vendor support, training
- Documentation and community resources
#2 — Palo Alto Networks Prisma Access
Short description : Provides secure access to applications and cloud resources with integrated ZTNA, SWG, and CASB capabilities for global enterprises.
Key Features
- Application segmentation
- Policy-based access controls
- Threat prevention and analytics
- Cloud-delivered ZTNA
- Centralized management
Pros
- Unified security stack
- Global reach for remote workforce
- Advanced analytics
Cons
- Premium cost
- Steeper learning curve
Platforms / Deployment
- Windows, macOS, Linux
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption
- GDPR, HIPAA
Integrations & Ecosystem
- SIEM, endpoint protection, SWG
- Cloud apps integration
Support & Community
- Vendor support
- Extensive documentation
#3 — Cisco Duo Beyond
Short description : Duo Beyond offers secure ZTNA access by enforcing device trust, user verification, and adaptive authentication.
Key Features
- Device and user verification
- Conditional access policies
- Endpoint health checks
- Single sign-on integration
- Threat detection
Pros
- Easy deployment for hybrid workforces
- Adaptive multi-factor authentication
- Strong visibility into endpoint posture
Cons
- Limited advanced analytics
- Enterprise features require additional licensing
Platforms / Deployment
- Windows, macOS, Linux, iOS, Android
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, RBAC
- SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Microsoft 365, Google Workspace, Okta
- Endpoint and SWG integration
- API support
Support & Community
- Vendor support
- Documentation and user community
#4 — Netskope Private Access
Short description : Extends CASB capabilities with ZTNA for private application access, combining security and zero trust policy enforcement.
Key Features
- Private app access
- Policy-based access controls
- Threat detection
- Cloud and on-premises support
- Real-time monitoring
Pros
- Unified CASB and ZTNA
- Cloud-native deployment
- Scalable for distributed teams
Cons
- High cost
- Requires training for full capabilities
Platforms / Deployment
- Windows, macOS
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption, RBAC
- GDPR, HIPAA
Integrations & Ecosystem
- SIEM, SWG, endpoint security
- Microsoft 365, Salesforce
Support & Community
- Vendor support
- Documentation
#5 — Akamai Enterprise Application Access
Short description : Akamai EAA secures applications with cloud-delivered ZTNA, ensuring secure access without exposing network resources.
Key Features
- Zero Trust access
- Application segmentation
- Threat analytics
- Adaptive access policies
- Global cloud delivery
Pros
- Cloud-native, scalable
- Reduces attack surface
- Integrates with identity providers
Cons
- Premium pricing
- Advanced configuration complexity
Platforms / Deployment
- Windows, macOS
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption
- GDPR, HIPAA
Integrations & Ecosystem
- Okta, Azure AD, Ping Identity
- API-based integrations
Support & Community
- Vendor support
- Documentation
#6 — Cloudflare Access
Short description : Cloudflare Access provides ZTNA for SaaS and internal applications with global edge enforcement and identity-based access.
Key Features
- Zero Trust policy enforcement
- Single sign-on integration
- Device posture assessment
- Real-time analytics
- Edge-based access control
Pros
- Fast, edge-distributed access
- Simplified deployment
- Integration with multiple identity providers
Cons
- Advanced enterprise features require add-ons
- Limited offline capabilities
Platforms / Deployment
- Windows, macOS, Linux
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption
- SOC 2, GDPR
Integrations & Ecosystem
- Microsoft 365, Okta, Google Workspace
- SIEM integration
- API support
Support & Community
- Vendor support
- Documentation and community forums
#7 — VMware Workspace ONE Access
Short description : Offers ZTNA and secure access for cloud and on-prem applications with device compliance checks.
Key Features
- Device and identity verification
- Conditional access policies
- Cloud and on-prem app support
- Unified endpoint management integration
- Policy enforcement
Pros
- Unified access across endpoints and apps
- Device posture awareness
- Scalable for enterprise deployments
Cons
- Complexity for SMBs
- Higher learning curve
Platforms / Deployment
- Windows, macOS, iOS, Android
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption
- GDPR, HIPAA
Integrations & Ecosystem
- VMware Horizon, Microsoft 365, Okta
- Endpoint management and SIEM
Support & Community
- Vendor support
- Documentation and community
#8 — Netskope ZTNA 2.0
Short description : Combines cloud-native ZTNA with CASB for adaptive, context-aware access to cloud and private apps.
Key Features
- Adaptive access policies
- Threat detection and DLP
- Cloud and private app coverage
- Real-time monitoring
- Granular access controls
Pros
- Cloud-native scalability
- Unified security stack
- Strong analytics
Cons
- Premium pricing
- Configuration complexity
Platforms / Deployment
- Windows, macOS
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption
- GDPR, HIPAA
Integrations & Ecosystem
- SIEM, SWG, endpoint protection
- Microsoft 365, Salesforce
Support & Community
- Vendor support
- Documentation
#9 — Palo Alto Networks Prisma SASE ZTNA
Short description : Integrates ZTNA with SASE for cloud and remote access, providing granular policy enforcement and secure connectivity.
Key Features
- SASE integration
- ZTNA access policies
- Threat analytics
- Cloud and SaaS coverage
- Real-time monitoring
Pros
- Unified SASE and ZTNA solution
- Enterprise scalability
- Strong analytics and reporting
Cons
- Costly for small deployments
- Complexity in configuration
Platforms / Deployment
- Windows, macOS, Linux
- Cloud
Security & Compliance
- SSO/SAML, MFA, encryption
- GDPR, HIPAA
Integrations & Ecosystem
- SIEM, CASB, endpoint security
- API connectors
Support & Community
- Vendor support
- Documentation
#10 — Citrix Gateway
Short description : Provides ZTNA for enterprise applications, integrating secure remote access with adaptive access policies.
Key Features
- Zero Trust access for apps
- Device and location-based policies
- Cloud and on-premise support
- Adaptive access controls
- Monitoring and analytics
Pros
- Supports hybrid environments
- Integration with Citrix ecosystem
- Scalable for large enterprises
Cons
- Premium pricing
- Complex deployment
Platforms / Deployment
- Windows, macOS, iOS, Android
- Cloud / Hybrid
Security & Compliance
- SSO/SAML, MFA, encryption
- GDPR, HIPAA
Integrations & Ecosystem
- Microsoft 365, Okta, VMware
- SIEM, SWG integration
Support & Community
- Vendor support
- Documentation
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Zscaler Private Access | Enterprise | Windows, macOS | Cloud | Cloud-native ZTNA | N/A |
| Prisma Access | Enterprise | Windows, macOS, Linux | Cloud | Unified security stack | N/A |
| Cisco Duo Beyond | SMB / Enterprise | Windows, macOS, Linux, iOS, Android | Cloud | Adaptive MFA + ZTNA | N/A |
| Netskope Private Access | Enterprise | Windows, macOS | Cloud | CASB + ZTNA | N/A |
| Akamai EAA | Enterprise | Windows, macOS | Cloud | Edge-based ZTNA | N/A |
| Cloudflare Access | SMB / Enterprise | Windows, macOS, Linux | Cloud | Edge enforcement | N/A |
| VMware Workspace ONE Access | Enterprise | Windows, macOS, iOS, Android | Cloud | Unified endpoint access | N/A |
| Netskope ZTNA 2.0 | Enterprise | Windows, macOS | Cloud | Adaptive access + CASB | N/A |
| Prisma SASE ZTNA | Enterprise | Windows, macOS, Linux | Cloud | ZTNA + SASE | N/A |
| Citrix Gateway | Enterprise | Windows, macOS, iOS, Android | Cloud / Hybrid | Adaptive remote access | N/A |
Evaluation & Scoring of ZTNA Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Zscaler Private Access | 9 | 8 | 9 | 9 | 9 | 8 | 7 | 8.4 |
| Prisma Access | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Cisco Duo Beyond | 8 | 8 | 8 | 8 | 8 | 7 | 7 | 7.9 |
| Netskope Private Access | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Akamai EAA | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Cloudflare Access | 7 | 8 | 7 | 7 | 7 | 7 | 7 | 7.1 |
| VMware Workspace ONE Access | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Netskope ZTNA 2.0 | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Prisma SASE ZTNA | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
| Citrix Gateway | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.7 |
Interpretation: Scores reflect comparative strengths in features, usability, integrations, security, performance, support, and overall value.
Which ZTNA Tool Is Right for You?
Solo / Freelancer
Cloud-native, lightweight ZTNA like Cloudflare Access offers secure, simple deployment for small teams.
SMB
Cisco Duo Beyond, Cloudflare Access, and Netskope ZTNA 2.0 provide adaptive access, threat protection, and SaaS coverage for growing organizations.
Mid-Market
Prisma Access, Akamai EAA, and VMware Workspace ONE Access deliver enterprise-grade ZTNA with compliance and policy automation.
Enterprise
Zscaler Private Access, Prisma SASE ZTNA, and Netskope Private Access provide global coverage, advanced analytics, and hybrid cloud integration.
Budget vs Premium
Lightweight deployments suit SMBs, premium tools offer enterprise-scale analytics, adaptive policies, and global coverage.
Feature Depth vs Ease of Use
SMBs prioritize deployment simplicity, enterprises require advanced analytics, adaptive policies, and hybrid coverage.
Integrations & Scalability
Enterprise deployments demand integration with SIEM, SWG, endpoint security, and identity providers, scaling for global users.
Security & Compliance Needs
Organizations in regulated sectors should ensure support for encryption, RBAC, audit logging, and compliance reporting for GDPR, HIPAA, SOC 2, and ISO 27001.
Frequently Asked Questions (FAQs)
1. What is ZTNA and how is it different from VPN?
ZTNA provides secure, least-privilege access based on user identity and context, whereas VPN grants broad network access.
2. How long does deployment take?
Cloud-native ZTNA deploys in days; enterprise hybrid deployments may take weeks.
3. Can ZTNA integrate with identity providers?
Yes, ZTNA integrates with SSO, MFA, and IAM solutions for adaptive access.
4. Are ZTNA solutions suitable for remote teams?
Yes, they provide secure access for remote and hybrid workers without exposing the network.
5. Do ZTNA solutions include threat analytics?
Most include user behavior monitoring, anomaly detection, and policy enforcement.
6. Can SMBs benefit from ZTNA?
Yes, cloud-native ZTNA like Cloudflare Access or Cisco Duo Beyond is scalable and cost-effective.
7. How does ZTNA support compliance?
By providing audit trails, access policies, and reporting for regulatory frameworks.
8. Does ZTNA protect cloud applications?
Yes, it enforces policy-based access to SaaS, IaaS, and on-prem applications.
9. Can ZTNA replace VPN entirely?
Yes, ZTNA is designed to replace legacy VPNs with granular, zero-trust access.
10. How to choose the right ZTNA tool?
Evaluate cloud adoption, compliance needs, user count, hybrid requirements, and integration with existing security infrastructure.
Conclusion
Zero Trust Network Access (ZTNA) is essential for modern security in hybrid and cloud-first organizations, providing granular, adaptive access, threat protection, and policy enforcement. SMBs benefit from lightweight tools like Cloudflare Access and Cisco Duo Beyond, while enterprises leverage Zscaler Private Access, Prisma SASE ZTNA, and Netskope Private Access for global, hybrid coverage. Organizations should assess access requirements, compliance mandates, and integrations, pilot shortlisted solutions, and implement them to secure applications and maintain a strong security posture.
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals