Introduction
Key Management Systems (KMS) are software solutions designed to create, store, rotate, and manage cryptographic keys securely. They are critical for enterprises to safeguard sensitive data, control access to encrypted information, and meet regulatory compliance requirements. With increasing adoption of cloud services, multi-cloud environments, and encryption across endpoints and applications, KMS has become a cornerstone of modern data security strategies.
Use cases for KMS include managing encryption keys for cloud storage, securing payment data, protecting customer information, enabling secure application communication, and automating cryptographic key lifecycle processes. Buyers evaluating KMS solutions should consider features like centralized key management, integration capabilities, compliance certifications, scalability, ease of use, monitoring, automation, and support for multi-cloud or hybrid environments.
Best for: Security teams, IT operations, compliance officers, enterprises handling sensitive financial, healthcare, or personal data.
Not ideal for: Small organizations with minimal sensitive data or those relying on built-in OS encryption without strict compliance needs.
Key Trends in Key Management Systems (KMS)
- AI-driven automation for key rotation and anomaly detection.
- Cloud-native KMS solutions integrated with major cloud providers.
- Support for hybrid and multi-cloud key management.
- Adoption of FIPS 140-2/3 and quantum-resistant encryption standards.
- Integration with SIEM, DLP, CASB, and identity management platforms.
- Centralized auditing and reporting for compliance purposes.
- Subscription-based KMS-as-a-Service models.
- End-to-end encryption support across applications, databases, and storage.
- Granular access control and role-based key access.
- Increased interoperability between on-prem and cloud security systems.
How We Selected These Tools (Methodology)
- Market adoption and vendor recognition.
- Completeness of key management features, including rotation, storage, and access control.
- Reliability, performance, and scalability indicators.
- Security posture and compliance certifications.
- Integration capabilities with cloud platforms, applications, and security ecosystems.
- Customer suitability for SMBs, mid-market, and enterprise organizations.
- Support quality, onboarding resources, and community engagement.
- Balance of cloud-native and on-premises solutions.
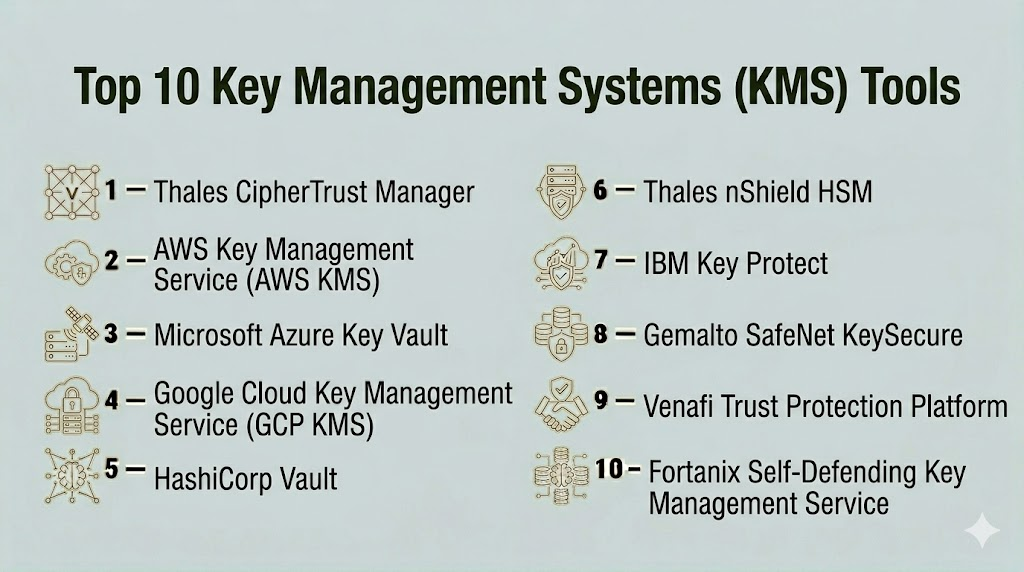
Top 10 Key Management Systems (KMS) Tools
#1 — Thales CipherTrust Manager
Short description: Thales CipherTrust Manager provides centralized key management and encryption across multi-cloud and hybrid environments. It is designed for enterprises requiring compliance, secure key lifecycle management, and broad integration options.
Key Features
- Centralized key lifecycle management
- Multi-cloud encryption support
- Hardware Security Module (HSM) integration
- Policy-driven access control
- Audit logging and reporting
- Tokenization support
- API-driven automation
Pros
- Comprehensive enterprise-grade KMS
- Strong compliance and regulatory support
- Scalable across hybrid and multi-cloud environments
Cons
- Complex deployment for smaller organizations
- Higher cost than entry-level KMS
Platforms / Deployment
- Cloud / Hybrid
- Web
Security & Compliance
- SOC 2, ISO 27001, GDPR
- SSO/SAML, MFA, encryption, RBAC
Integrations & Ecosystem
Integrates with AWS, Azure, Google Cloud, HSMs, SIEMs, and DevOps workflows.
- AWS KMS
- Azure Key Vault
- HSMs and security appliances
- SIEM platforms (Splunk, QRadar)
Support & Community
- Enterprise support tiers available
- Extensive documentation and community resources
#2 — AWS Key Management Service (KMS)
Short description: AWS KMS is a cloud-native key management solution for managing encryption keys for applications, data, and cloud services. Suitable for organizations already invested in the AWS ecosystem.
Key Features
- Managed key lifecycle
- Integrated with AWS services
- Automatic key rotation
- Detailed audit logs
- Policy-based key access
- Supports customer-managed and AWS-managed keys
Pros
- Fully integrated with AWS ecosystem
- Simplifies cloud encryption
- Highly scalable
Cons
- Limited to AWS environment
- Advanced enterprise features require higher tiers
Platforms / Deployment
- Cloud
- Web
Security & Compliance
- SOC 2, ISO 27001, GDPR
- MFA, encryption, RBAC
Integrations & Ecosystem
- AWS S3, RDS, Lambda, and other services
- API integration for custom applications
Support & Community
- AWS support tiers and documentation
- Large user community
#3 — Microsoft Azure Key Vault
Short description: Azure Key Vault secures cryptographic keys and secrets used by cloud applications, enabling centralized management and access policies within Microsoft Azure.
Key Features
- Key and secret management
- Certificate management
- Integration with Azure services
- Access policy and RBAC
- Audit and logging
- Automated key rotation
Pros
- Native Azure integration
- Simplified management for cloud apps
- Supports compliance and governance
Cons
- Limited use outside Azure
- Advanced features require higher pricing tiers
Platforms / Deployment
- Cloud
- Web
Security & Compliance
- SOC 2, ISO 27001, GDPR
- Encryption, RBAC, audit logs
Integrations & Ecosystem
- Azure App Services, Storage, SQL
- API for custom integrations
Support & Community
- Microsoft support
- Active community forums
#4 — Google Cloud Key Management Service
Short description: GCP KMS provides centralized key management for cloud applications and data, allowing secure encryption and policy-based access across Google Cloud.
Key Features
- Key lifecycle management
- Cloud-native integration
- Automated rotation and versioning
- HSM-backed keys
- Audit logging
- IAM-based access control
Pros
- Fully integrated with Google Cloud
- Simple key rotation and audit management
Cons
- Limited to GCP ecosystem
- Advanced features require enterprise licensing
Platforms / Deployment
- Cloud
- Web
Security & Compliance
- SOC 2, ISO 27001, GDPR
- Encryption, RBAC
Integrations & Ecosystem
- Google Cloud Storage, BigQuery, Compute Engine
- API access for custom apps
Support & Community
- Google Cloud support plans
- Active developer community
#5 — HashiCorp Vault
Short description: HashiCorp Vault is an open-source tool for managing secrets, tokens, and encryption keys across cloud and on-premise environments, with advanced policies and automation.
Key Features
- Secrets management
- Dynamic key generation
- Encryption-as-a-service
- Policy-based access control
- Audit logging
- Multi-cloud support
- API-driven integrations
Pros
- Flexible, developer-friendly
- Supports multi-cloud and hybrid
- Open-source with community support
Cons
- Steeper learning curve
- Enterprise features require paid edition
Platforms / Deployment
- Windows / Linux / macOS
- Cloud / Self-hosted / Hybrid
Security & Compliance
- SOC 2, ISO 27001
- Encryption, RBAC
Integrations & Ecosystem
- Terraform, Kubernetes, cloud providers
- API for DevOps workflows
Support & Community
- Enterprise support available
- Strong open-source community
#6 — Thales nShield HSM
Short description: Hardware Security Module (HSM) providing secure key storage and cryptographic operations for enterprise-grade KMS solutions.
Key Features
- Hardware-based key storage
- FIPS 140-2 certified
- High-performance encryption
- API access for applications
- Multi-tenant support
- Compliance reporting
Pros
- Strongest security guarantees
- Hardware-based protection
- Scalable performance
Cons
- Higher cost
- Requires physical deployment and maintenance
Platforms / Deployment
- On-premise / Hybrid
- Web
Security & Compliance
- FIPS 140-2, SOC 2, ISO 27001
- Encryption, audit logs
Integrations & Ecosystem
- Enterprise applications, cloud connectors
- API access
Support & Community
- Vendor support and documentation
#7 — IBM Key Protect
Short description: Cloud-based KMS for IBM Cloud that offers key lifecycle management, encryption, and access policies for cloud applications.
Key Features
- Key lifecycle management
- Integration with IBM Cloud services
- HSM-backed keys
- Audit logging
- Policy enforcement
Pros
- Cloud-native for IBM environment
- Simplified key management
- Compliance support
Cons
- Limited outside IBM Cloud
- Some advanced features require enterprise license
Platforms / Deployment
- Cloud
- Web
Security & Compliance
- SOC 2, ISO 27001, GDPR
- Encryption, RBAC
Integrations & Ecosystem
- IBM Cloud services
- APIs for custom apps
Support & Community
- IBM support tiers
- Documentation and forums
#8 — Gemalto SafeNet KeySecure
Short description: Enterprise KMS providing centralized key management and HSM integration for multi-cloud and on-prem environments.
Key Features
- Centralized key management
- Multi-cloud and hybrid support
- HSM integration
- Key lifecycle automation
- Compliance reporting
- API access
Pros
- Flexible enterprise deployment
- Strong compliance coverage
- Scalable
Cons
- Complex setup
- Enterprise pricing
Platforms / Deployment
- Windows / Linux / macOS
- Cloud / Hybrid / On-prem
Security & Compliance
- SOC 2, ISO 27001, GDPR
- Encryption, RBAC
Integrations & Ecosystem
- Cloud platforms, databases, applications
- API for automation
Support & Community
- Vendor support and knowledge base
#9 — Venafi Trust Protection Platform
Short description: Centralized key and certificate management for enterprises, supporting encryption, authentication, and compliance workflows.
Key Features
- Centralized key and certificate management
- Policy enforcement
- Audit reporting
- HSM and cloud integration
- API-driven automation
Pros
- Enterprise-scale
- Strong certificate lifecycle management
- Compliance support
Cons
- Higher complexity
- Premium pricing
Platforms / Deployment
- Cloud / Hybrid
- Web
Security & Compliance
- SOC 2, ISO 27001, GDPR
- Encryption, audit logs
Integrations & Ecosystem
- HSMs, cloud providers
- SIEM and DevOps platforms
Support & Community
- Enterprise support
- Documentation and resources
#10 — Fortanix Self-Defending Key Management Service
Short description: Provides secure, cloud-native key management with runtime encryption, secure enclaves, and integrated compliance reporting.
Key Features
- Runtime encryption
- Self-defending keys
- Centralized key management
- Audit and reporting
- Multi-cloud support
- API-driven integrations
Pros
- Advanced security with runtime protection
- Cloud-native and scalable
Cons
- Requires understanding of enclave technology
- Enterprise pricing
Platforms / Deployment
- Cloud / Hybrid
- Web
Security & Compliance
- SOC 2, ISO 27001, GDPR
- Encryption, RBAC
Integrations & Ecosystem
- Cloud platforms (AWS, Azure, GCP)
- APIs for DevOps workflows
Support & Community
- Vendor support
- Documentation available
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Thales CipherTrust | Enterprise | Web | Cloud / Hybrid | Centralized key management | N/A |
| AWS KMS | Cloud-native | Web | Cloud | AWS integration & auto-rotation | N/A |
| Azure Key Vault | Microsoft ecosystem | Web | Cloud | Policy-based access control | N/A |
| GCP KMS | Google Cloud | Web | Cloud | Cloud-native key management | N/A |
| HashiCorp Vault | Multi-cloud | Windows, Linux, macOS | Cloud / Hybrid / Self-hosted | Secrets management | N/A |
| Thales nShield HSM | Enterprise HSM | On-prem | On-prem / Hybrid | Hardware security | N/A |
| IBM Key Protect | IBM Cloud | Web | Cloud | HSM-backed keys | N/A |
| Gemalto SafeNet | Enterprise | Windows, Linux, macOS | Cloud / Hybrid / On-prem | Multi-cloud KMS | N/A |
| Venafi Trust Protection | Enterprise | Web | Cloud / Hybrid | Key & certificate management | N/A |
| Fortanix Self-Defending KMS | Cloud-native | Web | Cloud / Hybrid | Runtime protection & enclaves | N/A |
Evaluation & Scoring of Key Management Systems (KMS)
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Thales CipherTrust | 9 | 8 | 9 | 9 | 8 | 8 | 8 | 8.6 |
| AWS KMS | 8 | 9 | 8 | 8 | 8 | 9 | 8 | 8.3 |
| Azure Key Vault | 8 | 9 | 8 | 8 | 8 | 9 | 8 | 8.3 |
| GCP KMS | 8 | 8 | 8 | 8 | 8 | 8 | 8 | 8.0 |
| HashiCorp Vault | 9 | 7 | 9 | 8 | 8 | 8 | 8 | 8.2 |
| Thales nShield HSM | 9 | 7 | 8 | 9 | 9 | 8 | 7 | 8.3 |
| IBM Key Protect | 8 | 8 | 8 | 8 | 8 | 8 | 8 | 8.0 |
| Gemalto SafeNet | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.8 |
| Venafi Trust Protection | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.8 |
| Fortanix Self-Defending | 9 | 8 | 8 | 9 | 8 | 8 | 8 | 8.4 |
Scores are comparative and help assess feature depth, integrations, and security.
Which Key Management System (KMS) Tool Is Right for You?
Solo / Freelancer
- HashiCorp Vault or cloud-native AWS KMS for small-scale, flexible setups.
SMB
- Azure Key Vault or IBM Key Protect for moderate workloads with cloud integration.
Mid-Market
- Thales CipherTrust, Fortanix KMS for hybrid deployments and advanced policy management.
Enterprise
- Thales nShield HSM, Venafi Trust Protection, Gemalto SafeNet for large-scale encryption and compliance.
Budget vs Premium
- Budget: HashiCorp Vault, AWS KMS, Azure Key Vault
- Premium: Thales CipherTrust, nShield HSM, Venafi
Feature Depth vs Ease of Use
- Feature-rich: Thales CipherTrust, Fortanix
- Ease of use: AWS KMS, Azure Key Vault
Integrations & Scalability
- Multi-cloud integration: Thales CipherTrust, HashiCorp Vault
- Simple integration: Azure Key Vault, AWS KMS
Security & Compliance Needs
- Highest compliance: Thales nShield, Venafi
- Standard enterprise protection: HashiCorp Vault, IBM Key Protect
Frequently Asked Questions (FAQs)
1. What is a KMS?
A Key Management System is software that securely creates, stores, rotates, and manages encryption keys.
2. Why is KMS critical?
It ensures encryption keys are controlled, reducing the risk of data breaches and ensuring compliance.
3. Can KMS integrate with cloud applications?
Yes, most KMS solutions integrate with cloud platforms, databases, and applications via APIs.
4. What types of keys can KMS manage?
KMS manages symmetric, asymmetric, and HSM-backed keys for encryption, signing, and authentication.
5. Is KMS suitable for multi-cloud environments?
Yes, many modern KMS solutions support multi-cloud and hybrid deployments.
6. How does KMS support compliance?
By providing audit logs, key rotation policies, access control, and encryption standards adherence.
7. What is HSM integration?
Hardware Security Modules are physical devices used with KMS for secure key storage and high-assurance encryption.
8. How long does deployment take?
Deployment varies; cloud-native KMS can be operational in hours, enterprise-scale HSM deployments may take weeks.
9. Are open-source KMS solutions viable?
Yes, tools like HashiCorp Vault are robust, but enterprise features may require paid editions.
10. Can small businesses use KMS effectively?
Yes, cloud-native solutions like AWS KMS or Azure Key Vault are cost-effective and scalable for SMBs.
Conclusion
Key Management Systems (KMS) are foundational for modern encryption strategies, ensuring data remains secure across cloud, hybrid, and on-premise environments. Selecting the right KMS depends on organizational size, compliance requirements, deployment model, and integration needs. Enterprises may prefer Thales CipherTrust, nShield HSM, or Venafi for high-assurance security, while SMBs and mid-market organizations benefit from cloud-native options like AWS KMS, Azure Key Vault, or HashiCorp Vault. Organizations should shortlist tools, run pilot tests, and validate integrations and compliance adherence before full deployment.
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals