Introduction
Network configuration management is a specialized discipline within IT operations that focuses on the organized handling of a network’s lifecycle, from initial setup to ongoing maintenance and decommissioning. In plain English, it is the process of ensuring that every piece of hardware on a network—switches, routers, firewalls, and access points—is running the correct settings and software versions. Without a centralized system to manage these configurations, IT teams are forced to manually log into individual devices, a practice that is not only time-consuming but also prone to human error, which is the leading cause of network downtime.
In the current era of hyper-connectivity and hybrid work, the importance of this category has shifted from a convenience to a critical security requirement. Modern networks are no longer static; they are dynamic, software-defined environments that span across physical offices and multiple cloud providers. A single misconfiguration can open a massive security hole or take an entire global enterprise offline. Centralized configuration platforms provide the visibility needed to track who changed what, when they changed it, and how to revert to a “known good” state in seconds.
Real-world use cases for these platforms include:
- Disaster Recovery: Automatically restoring configuration files to new hardware after a primary device failure.
- Compliance Auditing: Running automated checks to ensure all devices meet regulatory standards like PCI-DSS, HIPAA, or SOC 2.
- Bulk Updates: Pushing a security patch or a password change to hundreds of devices simultaneously across different geographic locations.
- Vulnerability Management: Scanning firmware versions against known databases to identify hardware at risk of exploitation.
- Change Management: Keeping a complete history of every configuration change to satisfy internal governance and external auditors.
When evaluating these tools, buyers should assess:
- Multi-Vendor Support: The ability to manage hardware from different manufacturers (Cisco, Juniper, HP, etc.) through a single interface.
- Automation Capabilities: The depth of “no-code” or “low-code” workflows for repetitive tasks.
- Real-time Alerting: Immediate notification when an unauthorized configuration change is detected.
- Baseline Comparisons: Tools to compare current settings against a “Golden Configuration.”
- Role-Based Access Control (RBAC): Granular permissions to ensure only authorized personnel can make changes.
- Scalability: How well the system handles an increase in the number of managed nodes.
- Integration Ecosystem: Connectivity with ITSM platforms and monitoring suites.
- Security Auditing: Built-in templates for common security frameworks and hardening guides.
Best for: IT managers, network engineers, security operations teams, and MSPs overseeing complex, multi-site infrastructures.
Not ideal for: Small home offices with a single router, or tiny businesses where the network hardware is provided and managed entirely by an ISP.
Key Trends in Network Configuration Management
- Infrastructure as Code (IaC) Integration: Modern platforms are moving toward declarative models where network state is defined in text files, allowing for version control and automated testing similar to software development.
- AI-Driven Intent-Based Networking: Systems are becoming “intent-aware,” where an administrator specifies a desired outcome (e.g., “isolate guest traffic”) and the AI calculates and pushes the necessary configuration changes across the entire fabric.
- Self-Healing Networks: Advanced platforms can now detect a configuration-related performance dip and automatically roll back to the previous stable version without human intervention.
- Vendor-Agnostic Standardization: As organizations move away from single-vendor lock-in, there is a massive trend toward tools that use standardized protocols like Netconf and Restconf to manage diverse hardware.
- Zero-Trust Network Access (ZTNA) Alignment: Configuration tools are now playing a vital role in security by automatically enforcing granular access policies at the port level based on user identity.
- Cloud-Managed Network Control: A shift from heavy on-premises management servers to cloud-native platforms that provide global visibility through a single browser-based dashboard.
- Automated Compliance Remediation: Systems no longer just “report” on a compliance failure; they can now be set to automatically “fix” the setting back to the required standard.
- Predictive Change Analysis: Using digital twins to simulate a configuration change in a virtual environment to predict its impact on traffic flow before pushing it to production hardware.
How We Selected These Tools (Methodology)
To identify the top platforms for the modern network landscape, we applied a comprehensive selection framework:
- Market Adoption and Reliability: We prioritized tools with high “mindshare” and a proven track record in enterprise environments.
- Feature Completeness: Selection was weighted toward platforms that offer end-to-end management, from backup and restore to advanced automation and compliance.
- Multi-Vendor Versatility: We looked for software that successfully manages diverse hardware ecosystems rather than just a single manufacturer’s line.
- Security Posture: Evaluation included the robustness of the platform’s own security, including encryption standards and access controls.
- Performance Signals: Analysis of how the tools handle high-latency or low-bandwidth connections to remote sites.
- Customer Fit Across Segments: We ensured the list includes options for small businesses (SMBs), global enterprises, and developer-first organizations.
- Ease of Use vs. Technical Depth: We balanced tools that offer simple “point-and-click” interfaces with those that provide deep, scriptable power for advanced engineers.
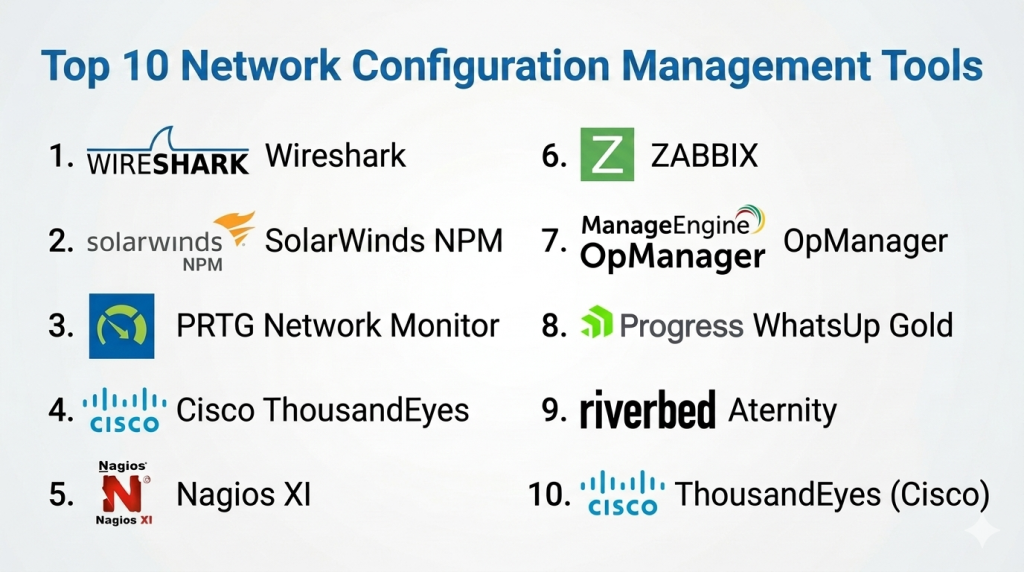
Top 10 Network Configuration Management Tools
1 — SolarWinds Network Configuration Manager
SolarWinds NCM is a cornerstone of enterprise network management, designed to automate the heavy lifting of configuration backups, change monitoring, and compliance auditing. It is particularly effective for large organizations that need to maintain a “Golden Configuration” across thousands of devices.
Key Features
- Automated Configuration Backups: Schedule regular backups of device settings to ensure a quick recovery in case of hardware failure.
- Real-Time Change Alerts: Immediate notification via email or dashboard when a change is detected on a monitored node.
- Vulnerability Integration: Native integration with the National Vulnerability Database to identify at-risk firmware versions.
- Compliance Auditing: Built-in templates for PCI, HIPAA, and DISA STIG to automate the reporting process.
- Bulk Change Deployment: Execute scripts across multiple devices simultaneously to update passwords or security policies.
Pros
- Exceptional multi-vendor support covering hundreds of hardware types.
- User-friendly interface that simplifies complex compliance reporting.
Cons
- Can be resource-intensive, requiring a robust server for optimal performance.
- The licensing model can become expensive as the network scales.
Platforms / Deployment
- Windows
- Self-hosted / Hybrid
Security & Compliance
- SSO/SAML, MFA, RBAC
- FIPS 140-2, SOC 2 compliant (SolarWinds Enterprise)
Integrations & Ecosystem
NCM is part of the broader SolarWinds Orion Platform, allowing for deep data sharing with performance monitoring tools.
- SolarWinds Network Performance Monitor (NPM)
- ServiceNow
- Cisco, Juniper, HP, Dell
- Aruba, Palo Alto
Support & Community
Access to the THWACK community with thousands of shared device templates and 24/7 technical support for active subscribers.
2 — ManageEngine Network Configuration Manager
ManageEngine provides a comprehensive and budget-friendly solution for managing the configuration lifecycle. It is highly regarded by SMBs and mid-market companies for its rapid deployment and intuitive dashboard.
Key Features
- Configuration Versioning: Keep a detailed history of all changes, allowing for side-by-side comparisons of different versions.
- Role-Based Access Control: Define exactly who can view, edit, or deploy configurations to prevent unauthorized access.
- Configlets: Use pre-defined command templates to execute common tasks without writing scripts from scratch.
- Compliance Management: Automatically check configurations against a set of standards and generate “Pass/Fail” reports.
- Remote Management: Securely manage devices in different geographic locations via a single central console.
Pros
- Very intuitive setup that allows teams to start backing up devices within minutes.
- Affordable pricing tiers compared to other enterprise-level competitors.
Cons
- The web interface can feel cluttered when managing a very high volume of nodes.
- Some advanced automation features require more manual scripting than high-end tools.
Platforms / Deployment
- Web / Windows / Linux
- Cloud / Self-hosted
Security & Compliance
- RBAC, AES encryption, Audit logs
- GDPR compliant
Integrations & Ecosystem
ManageEngine offers a tightly knit ecosystem of IT management tools.
- ManageEngine OpManager
- ManageEngine ServiceDesk Plus
- Zendesk
- Active Directory
Support & Community
A dedicated customer support portal, extensive video tutorials, and an active user forum for troubleshooting.
3 — Cisco Prime Infrastructure
Cisco Prime is a specialized management suite designed specifically for Cisco-heavy environments. It provides deep, granular control over the wired and wireless lifecycle within a single platform.
Key Features
- Converged Management: Manage both wired and wireless infrastructure from a single unified dashboard.
- Configuration Templates: Leverage Cisco-validated designs to deploy best-practice settings across the network.
- Automated Discovery: Quickly identify new Cisco hardware on the network and bring it under management.
- Compliance Reports: Specific auditing for Cisco-specific security advisories and hardening guides.
- Application Visibility: Monitor how configuration changes impact the performance of critical business applications.
Pros
- Deepest possible integration for Cisco hardware, including advanced features other tools might miss.
- Excellent for managing large-scale wireless deployments (Access Points and Controllers).
Cons
- Limited functionality for non-Cisco hardware, leading to a “siloed” management experience.
- Steep learning curve due to the complexity and depth of the feature set.
Platforms / Deployment
- Linux (Virtual Appliance)
- Self-hosted / Hybrid
Security & Compliance
- TACACS+, RADIUS, RBAC
- Not publicly stated
Integrations & Ecosystem
Cisco Prime is designed to work within the broader Cisco DNA and ISE security frameworks.
- Cisco Identity Services Engine (ISE)
- Cisco DNA Center
- ServiceNow
- Splunk
Support & Community
Access to the Cisco Technical Assistance Center (TAC) and a massive global network of certified Cisco engineers.
4 — Ansible (Red Hat)
Ansible has revolutionized network management by treating configurations as code. It is the go-to tool for DevOps-oriented teams who want to automate their infrastructure using simple, human-readable YAML files.
Key Features
- Agentless Architecture: Manages devices over standard SSH or APIs without needing to install software on the hardware.
- Playbooks: Create reusable scripts that define the “state” of the network, making it easy to replicate environments.
- Inventory Management: Group devices by function or location to apply configurations selectively.
- Idempotency: Ensures that the software only makes changes if the current state differs from the desired state.
- Large Module Library: Thousands of pre-built modules for virtually every network vendor on the market.
Pros
- Extremely flexible and powerful for building custom automation workflows.
- No licensing fees for the open-source version, though the enterprise version (Automation Platform) is paid.
Cons
- Requires a strong understanding of command-line interfaces and YAML syntax.
- Lacks the “out-of-the-box” GUI for backups and compliance reporting found in specialized tools.
Platforms / Deployment
- Linux / macOS
- Self-hosted / Cloud (Automation Platform)
Security & Compliance
- SSO/SAML, RBAC, Vault for secret management
- SOC 2, ISO 27001 (Automation Platform)
Integrations & Ecosystem
Ansible is the “connective tissue” for the modern infrastructure stack.
- GitHub / GitLab
- ServiceNow
- Terraform
- Cisco, Juniper, Arista, Palo Alto
Support & Community
A massive open-source community on GitHub and professional enterprise support provided by Red Hat.
5 — Netwrix Auditor for Network Devices
Netwrix focuses heavily on the security and auditing side of configuration management. It is designed for organizations that need to maintain a strict audit trail for compliance and security investigations.
Key Features
- Configuration Change Tracking: Provides a clear “Before” and “After” view of every change made to a device.
- User Activity Auditing: Shows exactly who logged into a device and what commands they executed.
- Alerting on Critical Changes: Immediate alerts for high-risk actions, such as disabling a firewall rule or changing an admin password.
- Compliance Assessment: Maps configuration changes directly to specific regulatory controls.
- Long-term Archive: Keeps an audit trail for years to satisfy long-term regulatory requirements.
Pros
- Exceptional for security forensics and demonstrating compliance to external auditors.
- Very clear and easy-to-read reports that non-technical stakeholders can understand.
Cons
- Focuses more on “Auditing” than the “Action” of deploying configuration changes.
- Less robust for bulk automation compared to tools like Ansible or SolarWinds.
Platforms / Deployment
- Windows
- Self-hosted / Hybrid
Security & Compliance
- SSO/SAML, RBAC, MFA
- SOC 2, ISO 27001 compliant
Integrations & Ecosystem
Netwrix is built to integrate with broader enterprise security ecosystems.
- Active Directory
- Splunk
- ServiceNow
- Cisco, Fortinet, SonicWall
Support & Community
Strong professional support and a comprehensive knowledge base for configuration and security best practices.
6 — Progress WhatsUp Gold
WhatsUp Gold is known for its visual approach to network management. It provides a highly interactive map that allows administrators to manage configurations directly from a visual representation of their network.
Key Features
- Interactive Topology Maps: Visualize your entire network and see the configuration status of each device in real-time.
- Configuration Compliance: Automatically scan devices to ensure they are using the latest approved firmware and settings.
- Automated Backups: Set recurring schedules to capture and store configuration files safely.
- Alert Center: A centralized hub for all notifications, including performance dips and unauthorized configuration changes.
- Custom Reporting: Create drag-and-drop reports to share with management or audit teams.
Pros
- The visual interface is one of the best in the industry for quickly identifying problem areas.
- Lower barrier to entry for junior administrators compared to more technical suites.
Cons
- Advanced automation scripts can be more difficult to implement than in code-first tools.
- Multi-vendor support is good but not as deep as specialized enterprise managers.
Platforms / Deployment
- Windows
- Self-hosted / Hybrid
Security & Compliance
- RBAC, TLS encryption, Audit logs
- Not publicly stated
Integrations & Ecosystem
Focuses on general network and server monitoring connectivity.
- ServiceNow
- Slack
- Opsgenie
- Microsoft Teams
Support & Community
A well-regarded customer success program and a community forum with shared templates and scripts.
7 — Micro Focus (OpenText) Network Node Manager i
NNMi is an enterprise-grade platform built for massive, high-performance networks. It is designed to handle the complexity of global corporations where network availability is tied directly to revenue.
Key Features
- Dynamic Discovery: Continuously discovers and maps the network as it changes, including physical and virtual links.
- Causal Analysis: Uses a sophisticated engine to identify the root cause of network issues rather than just reporting symptoms.
- Configuration & Compliance (NCC): An integrated module that provides deep policy-based configuration management.
- Scalable Architecture: Designed to manage tens of thousands of nodes across a distributed global footprint.
- Smart Plug-ins: Specialized modules to extend management into MPLS, IP Telephony, and Multicast environments.
Pros
- Extremely powerful for large-scale, complex environments with diverse networking technologies.
- Sophisticated logic for preventing “alert storms” during a major outage.
Cons
- One of the most complex and expensive tools to deploy and maintain.
- Requires significant training and dedicated personnel to manage effectively.
Platforms / Deployment
- Linux / Windows
- Self-hosted / Hybrid
Security & Compliance
- SSO/SAML, RBAC, FIPS 140-2
- SOC 2, ISO 27001 compliant (OpenText Enterprise)
Integrations & Ecosystem
NNMi is a cornerstone of the OpenText IT Operations Management (ITOM) suite.
- ServiceNow
- Micro Focus Operations Bridge
- Cisco, Juniper, Arista
- HPE
Support & Community
High-end enterprise support and a global user community through the Vivit user group.
8 — BackBox
BackBox is a specialized platform that focuses on automation for network and security devices. It is particularly strong in the “Security Operations” niche, emphasizing disaster recovery and backup.
Key Features
- Multi-Vendor Backup: Supports over 180 different vendors, including many niche security and firewall products.
- Automated Verification: Not only backs up the configuration but also verifies that the backup is valid and usable.
- Custom Task Automation: A flexible engine for automating complex multi-step tasks across diverse hardware.
- Disaster Recovery: A streamlined process for pushing configurations to new hardware in emergency scenarios.
- Inventory Management: Automatically gathers detailed hardware specs, including serial numbers and license info.
Pros
- If you have a large variety of different security appliances, BackBox likely has the best support.
- Focus on “Backup Verification” provides a much higher level of confidence than standard backup tools.
Cons
- Less focus on general performance monitoring than some of the “all-in-one” suites.
- The UI is functional but feels more like a technical utility than a modern SaaS dashboard.
Platforms / Deployment
- Linux (Virtual Appliance)
- Self-hosted / Cloud / Hybrid
Security & Compliance
- RBAC, TLS encryption, MFA
- Not publicly stated
Integrations & Ecosystem
BackBox acts as a bridge between diverse network hardware and high-level management tools.
- Splunk
- ServiceNow
- Cisco, Fortinet, Check Point, F5
- Palo Alto
Support & Community
Direct access to technical engineers and a very responsive support model for custom vendor requests.
9 — Juniper Networks Paragon Automation
Paragon Automation is a modern, AI-driven suite designed for the next generation of cloud-era networking. It focuses heavily on network “assurance” and intent-based operations.
Key Features
- Intent-Based Orchestration: Translate business requirements into network configurations automatically across the fabric.
- Active Assurance: Uses synthetic traffic to verify that the network is actually performing as the configuration intended.
- Device Lifecycle Management: Automates the “Day 0” to “Day N” lifecycle of Juniper hardware.
- HealthBot: A diagnostics and analytics tool that uses AI to predict and prevent configuration-related issues.
- Cloud-Native Microservices: A flexible architecture that can be deployed across private and public clouds.
Pros
- The most forward-thinking tool for organizations moving toward “Autonomous Networks.”
- Unrivaled visibility and testing for Juniper-centric service provider environments.
Cons
- Primarily focused on Juniper hardware, though it can manage others through standard protocols.
- High technical complexity; best suited for Tier-1 service providers and large enterprises.
Platforms / Deployment
- Linux (Kubernetes)
- Cloud / Hybrid
Security & Compliance
- SSO/SAML, RBAC, Certificate-based auth
- Not publicly stated
Integrations & Ecosystem
Deeply integrated into the Juniper ecosystem and standard open protocols.
- Juniper Mist AI
- Netconf / Restconf
- ServiceNow
- Splunk
Support & Community
Premier support through Juniper Care and a highly technical community for network automation experts.
10 — Nautobot (Network to Code)
Nautobot is an open-source “Network Source of Truth” and automation platform. It is designed to be the central database that defines what the network should look like.
Key Features
- Source of Truth: Acts as the definitive record for all IP addresses, device roles, and configurations.
- App Ecosystem: Allows developers to build custom apps on top of the network data to automate specific workflows.
- Extensible Data Model: Easily add custom fields and relationships to track information unique to your organization.
- Webhooks & API: Trigger external actions automatically whenever data in the source of truth changes.
- Config Contexts: Manage hierarchical configuration data that can be used to generate device-specific settings.
Pros
- The gold standard for organizations moving toward a “Code-First” network strategy.
- Highly flexible and community-driven, with no vendor lock-in.
Cons
- Requires a team with Python and developer skills to unlock its full potential.
- Does not “push” configurations by default; it is intended to work with a separate executor like Ansible.
Platforms / Deployment
- Linux (Docker/Kubernetes)
- Self-hosted / Cloud / Hybrid
Security & Compliance
- RBAC, Token-based API auth, SSO
- Not publicly stated
Integrations & Ecosystem
Nautobot is the centerpiece of the modern network automation toolchain.
- Ansible
- Terraform
- Cisco, Arista, Juniper
- ServiceNow / Jira
Support & Community
A thriving open-source community on Slack and GitHub, with professional support available through Network to Code.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
| SolarWinds NCM | Large Multi-Vendor Enterprise | Win | Hybrid | Vulnerability Integration | N/A |
| ManageEngine NCM | SMB & Rapid Deployment | Win/Linux | Cloud/Self | Configuration Configlets | N/A |
| Cisco Prime | Cisco-Only Ecosystems | Linux | Self-hosted | Wired/Wireless Convergence | N/A |
| Ansible | DevOps & Code-First Teams | Linux/macOS | Cloud/Self | Agentless YAML Playbooks | N/A |
| Netwrix Auditor | Security & Forensic Auditing | Win | Hybrid | Before/After Visual Delta | N/A |
| WhatsUp Gold | Visual Network Management | Win | Hybrid | Interactive Topology Maps | N/A |
| OpenText NNMi | High-Performance Global Ops | Win/Linux | Hybrid | Causal Root Cause Analysis | N/A |
| BackBox | Security & Disaster Recovery | Linux | Cloud/Self | Automated Backup Verification | N/A |
| Juniper Paragon | AI-Driven Assurance | Linux | Cloud/Self | Active Traffic Assurance | N/A |
| Nautobot | Network Source of Truth | Linux | Cloud/Self | Extensible Data App Model | N/A |
Evaluation & Scoring of Network Configuration Management
The following scoring model represents a comparative analysis of how these tools perform in modern technical environments.
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
| SolarWinds NCM | 9 | 7 | 10 | 9 | 8 | 9 | 7 | 8.4 |
| ManageEngine NCM | 8 | 9 | 8 | 8 | 8 | 8 | 9 | 8.2 |
| Cisco Prime | 10 | 4 | 7 | 9 | 9 | 9 | 6 | 7.6 |
| Ansible | 10 | 5 | 10 | 9 | 10 | 7 | 10 | 8.8 |
| Netwrix Auditor | 7 | 8 | 8 | 10 | 9 | 8 | 8 | 8.2 |
| WhatsUp Gold | 7 | 10 | 8 | 8 | 8 | 8 | 8 | 8.1 |
| OpenText NNMi | 10 | 3 | 9 | 9 | 10 | 9 | 6 | 7.9 |
| BackBox | 8 | 7 | 7 | 9 | 9 | 8 | 8 | 7.9 |
| Juniper Paragon | 10 | 4 | 8 | 9 | 9 | 9 | 7 | 7.9 |
| Nautobot | 9 | 5 | 10 | 8 | 10 | 7 | 10 | 8.5 |
How to interpret the scores
- Technical Power vs. Accessibility: Tools like Ansible and Nautobot score high on technical “Core” and “Performance” but lower on “Ease of Use” because they require coding skills.
- Security Focus: Netwrix and SolarWinds lead in security-specific features and compliance reporting.
- Integration Strength: Modern code-first tools (Ansible, Nautobot) lead in integration because they can be easily “plugged in” to broader automated workflows.
Which Network Configuration Management Tool Is Right for You?
Solo / Freelancer
If you are an independent network consultant, Ansible is your best bet. It allows you to build a library of “Playbooks” that you can take from client to client, automating the setup of new networks without recurring licensing fees.
SMB
Small-to-medium businesses should look toward ManageEngine NCM. It provides the most “bang for the buck” and doesn’t require a dedicated team of engineers to maintain the management software itself.
Mid-Market
For companies with several hundred devices and a mix of vendors, SolarWinds NCM or WhatsUp Gold provide a good balance of professional features and ease of use. SolarWinds is better for compliance, while WhatsUp Gold is better for visual troubleshooting.
Enterprise
Large-scale corporations with strict compliance and security needs should focus on SolarWinds NCM or OpenText NNMi. These tools offer the scalability and high-level reporting that executive teams and auditors require.
Budget vs Premium
Ansible (Open Source) is the ultimate budget choice, costing nothing in licensing. On the premium end, Juniper Paragon and Cisco Prime provide the highest level of vendor-specific depth for organizations that have invested heavily in those hardware ecosystems.
Feature Depth vs Ease of Use
WhatsUp Gold is the easiest to use due to its visual nature. On the other end, Nautobot offers the most feature depth for customization but requires a significant technical investment to master.
Integrations & Scalability
Ansible and Nautobot lead in this category. Because they are code-centric, they can scale to manage virtually any number of devices and integrate into any modern CI/CD pipeline.
Security & Compliance Needs
Netwrix Auditor is the premier choice for organizations where “Auditing” is the top priority. If you need to “Action” those audits (i.e., fix the configurations), SolarWinds NCM is the better choice.
Frequently Asked Questions (FAQs)
1. What is a “Golden Configuration” in network management?
A Golden Configuration is a standardized, “best-practice” configuration file that has been tested and approved. It serves as the baseline that all similar devices on the network should match to ensure security and performance.
2. How often should I back up my network configurations?
Most experts recommend backing up configurations whenever a change is made. High-end tools can do this automatically by detecting a “config change” syslog message and triggering an immediate backup.
3. Can I use these tools to manage cloud firewalls and virtual routers?
Yes, modern platforms like Ansible, Nautobot, and SolarWinds have specific modules to manage virtualized network instances in AWS, Azure, and Google Cloud alongside physical hardware.
4. What is the difference between “monitoring” and “configuration management”?
Monitoring tracks the health and traffic of a device (e.g., Is it up? How much bandwidth is being used?). Configuration management focuses on the settings (e.g., What is the admin password? What firewall rules are active?).
5. Do these tools support hardware from different vendors?
Most do. Tools like ManageEngine and SolarWinds support hundreds of vendors. However, some tools like Cisco Prime are highly specialized and only offer basic management for non-Cisco hardware.
6. How does a configuration manager help during a security breach?
It allows you to quickly see what changed right before the breach occurred. It also enables you to “roll back” all devices to a clean configuration to ensure no backdoors or unauthorized rules were left behind by an attacker.
7. What is “Idempotency” in network automation?
Idempotency is a property of tools like Ansible where running a script multiple times will only make changes if the device is not already in the desired state. This prevents accidental duplicate commands or reboots.
8. Is it possible to automate firmware updates across the whole network?
Yes, enterprise configuration managers can push firmware images to hundreds of devices at once and schedule a reboot during a maintenance window, significantly reducing the manual labor involved in patching.
9. What are “Configlets” in ManageEngine NCM?
Configlets are small, reusable snippets of configuration code. They allow you to apply specific settings (like a new DNS server address) to multiple devices without needing to push a whole new configuration file.
10. Do I need to be a programmer to use these tools?
No. Tools like SolarWinds and WhatsUp Gold are designed for point-and-click use. However, if you want to use code-first tools like Ansible or Nautobot, a basic understanding of YAML and Python is very helpful.
Conclusion
Effective network configuration management is the difference between a secure, resilient infrastructure and one that is constantly plagued by “mysterious” outages and security gaps. Whether you are a small team looking for the rapid deployment of ManageEngine or a large enterprise building a code-first “Source of Truth” with Nautobot, the goal is the same: eliminate manual error and provide a clear audit trail.Your next step should be to run a small pilot with 2-3 of these tools to see how well they handle your specific hardware mix. Focus on the ease of the “Backup and Restore” process first, as this is the most critical function in a disaster scenario. Once that is locked in, you can begin exploring the advanced automation and compliance features to further secure your network.
Find Trusted Cardiac Hospitals
Compare heart hospitals by city and services — all in one place.
Explore Hospitals